-
k8s审计
介绍
Kubernetes 审计(Auditing) 功能提供了与安全相关的、按时间顺序排列的记录集, 记录每个用户、使用 Kubernetes API 的应用以及控制面自身引发的活动。
审计功能使得集群管理员能够回答以下问题:
- 发生了什么?
- 什么时候发生的?
- 谁触发的?
- 活动发生在哪个(些)对象上?
- 在哪观察到的?
- 它从哪触发的?
- 活动的后续处理行为是什么?
审计记录最初产生于 kube-apiserver 内部。每个请求在不同执行阶段都会生成审计事件;这些审计事件会根据特定策略 被预处理并写入后端。策略确定要记录的内容和用来存储记录的后端。 当前的后端支持日志文件和 webhook。
审计阶段
每个请求都可被记录其相关的 阶段(stage)。已定义的阶段有:
- RequestReceived - 一旦接收到请求即刻记录审计事件。
- ResponseStarted - 响应头发出,响应消息体未发出之前,一般适用于长连接或者耗时任务的场景。
- ResponseComplete - 当响应消息体完成。
- Panic - 当 panic 发生时生成。
审计日志记录功能会增加 API server 的内存消耗,因为需要为每个请求存储审计所需的某些上下文。 此外,内存消耗取决于审计日志记录的配置。
审计策略
审计政策定义了关于应记录哪些事件以及应包含哪些数据的规则。 审计策略对象结构定义在 audit.k8s.io 的API组中。
审计级别
处理事件时,将按顺序与规则列表进行比较。第一个匹配规则设置事件的审计级别(Audit Level)。已定义的审计级别有:
- None - 符合这条规则的日志将不会记录。
- Metadata - 记录请求的元数据(请求的用户、时间戳、资源、动词等等), 但是不记录请求或者响应的消息体。
- Request - 记录事件的元数据和请求的消息体,但是不记录响应的消息体。 这不适用于非资源类型的请求。
- RequestResponse - 记录事件的元数据,请求和响应的消息体。这不适用于非资源类型的请求。
也可以使用 --audit-policy-file 标志将包含策略的文件传递给 kube-apiserver。 如果不设置该参数,则不记录事件。 注意 rules 字段必须在审计策略文件中提供。
审计后端
审计后端实现将审计事件导出到外部存储。Kube-apiserver 默认提供两个后端:
- Log 后端,将事件写入到文件系统。
- –audit-log-path 指定用来写入审计事件的日志文件路径。不指定此标志会禁用日志后端。- 意味着标准化
- –audit-log-maxage 定义保留旧审计日志文件的最大天数
- –audit-log-maxbackup 定义要保留的审计日志文件的最大数量
- –audit-log-maxsize 定义审计日志文件的最大大小(兆字节)
- Webhook 后端,将事件发送到外部 HTTP API。
Webhook 配置文件使用 kubeconfig 格式指定服务的远程地址和用于连接它的凭据。- –audit-webhook-config-file 设置 Webhook 配置文件的路径。Webhook 配置文件实际上是一个 kubeconfig 文件。
–audit-webhook-initial-backoff 指定在第一次失败后重发请求等待的时间。随后的请求将以指数退避重试。
- –audit-webhook-config-file 设置 Webhook 配置文件的路径。Webhook 配置文件实际上是一个 kubeconfig 文件。
实例
创建审计策略文件
cd /etc/kubernetes vim audit-policy.yaml apiVersion: audit.k8s.io/v1 # This is required. kind: Policy # Don't generate audit events for all requests in RequestReceived stage. omitStages: - "RequestReceived" rules: # Log pod changes at RequestResponse level - level: RequestResponse resources: - group: "" # Resource "pods" doesn't match requests to any subresource of pods, # which is consistent with the RBAC policy. resources: ["pods"] # Log "pods/log", "pods/status" at Metadata level - level: Metadata resources: - group: "" resources: ["pods/log", "pods/status"] # Don't log requests to a configmap called "controller-leader" - level: None resources: - group: "" resources: ["configmaps"] resourceNames: ["controller-leader"] # Don't log watch requests by the "system:kube-proxy" on endpoints or services - level: None users: ["system:kube-proxy"] verbs: ["watch"] resources: - group: "" # core API group resources: ["endpoints", "services"] # Don't log authenticated requests to certain non-resource URL paths. - level: None userGroups: ["system:authenticated"] nonResourceURLs: - "/api*" - "/version" # Log the request body of configmap changes in kube-system. - level: Request resources: - group: "" # core API group resources: ["configmaps"] # This rule only applies to resources in the "kube-system" namespace. # The empty string "" can be used to select non-namespaced resources. namespaces: ["kube-system"] # Log configmap and secret changes in all other namespaces at the Metadata level. - level: Metadata resources: - group: "" # core API group resources: ["secrets", "configmaps"] # Log all other resources in core and extensions at the Request level. - level: Request resources: - group: "" # core API group - group: "extensions" # A catch-all rule to log all other requests at the Metadata level. - level: Metadata # Long-running requests like watches that fall under this rule will not # generate an audit event in RequestReceived. omitStages: - "RequestReceived"- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
可以使用最低限度的审计策略文件在 Metadata 级别记录所有请求:
# 在 Metadata 级别为所有请求生成日志 apiVersion: audit.k8s.io/v1beta1 kind: Policy rules: - level: Metadata- 1
- 2
- 3
- 4
- 5
开启审计
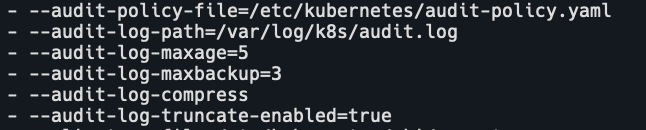
vim /etc/kubernetes/manifests/kube-apiserver.yaml - --audit-policy-file=/etc/kubernetes/audit-policy.yaml # 指定用来写入审计事件的日志文件路径。不指定此标志会禁用日志后端。 - --audit-log-path=/var/log/audit.log # 定义审计日志文件的最大大小(兆字节) - --audit-log-maxsize=100 # 定义了保留旧审计日志文件的最大天数 - --audit-log-maxage=5 # 定义了要保留的审计日志文件的最大数量 - --audit-log-maxbackup=3 # 开启日志压缩 - --audit-log-compress # 开启截断 - --audit-log-truncate-enabled=true- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
挂载数据卷
volumeMounts: - mountPath: /etc/kubernetes/audit-policy.yaml name: audit readOnly: true - mountPath: /var/log/k8s name: audit-log- 1
- 2
- 3
- 4
- 5
- 6

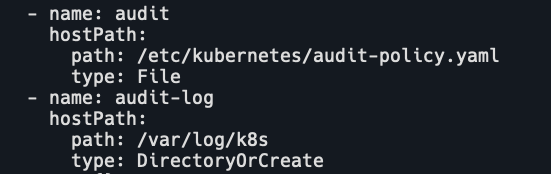
配置 hostPath
- name: audit hostPath: path: /etc/kubernetes/audit-policy.yaml type: File - name: audit-log hostPath: path: /var/log/k8s type: DirectoryOrCreate- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
保存后等待apiserver重启完成。
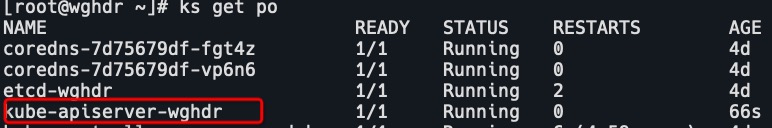
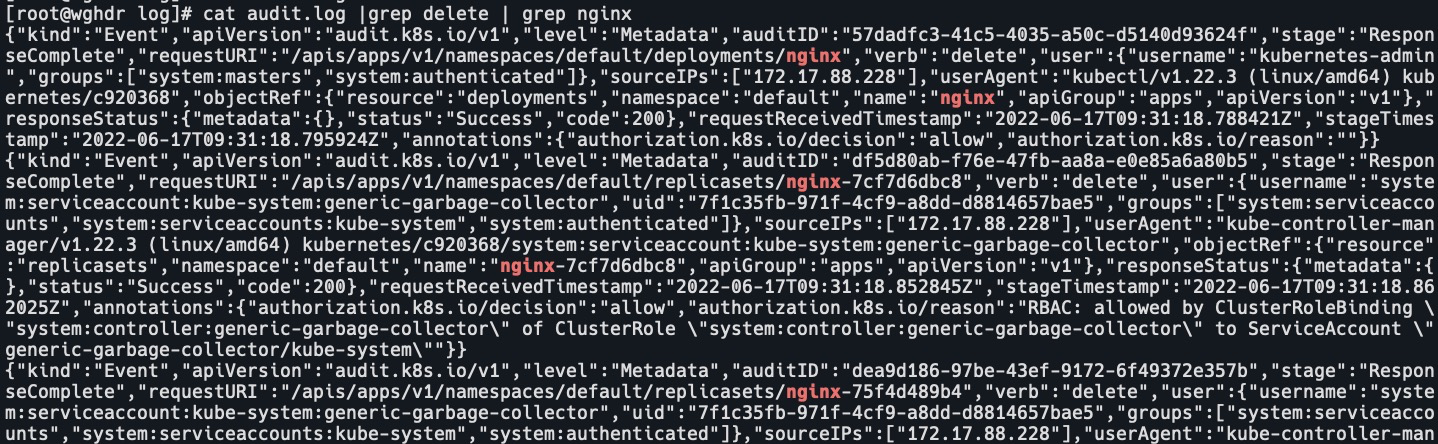
测试启动,删除pod,查看日志

日志轮转
我这里审计日志没有自动轮转,而是到了100m后日志就不动了。查看apiserver日志有如下报错:

使用logrotate
yum -y install logrotate- 1
定义audit配置文件
cat /etc/logrotate.d/audit /var/log/k8s/audit.log { # 指定文件属性 create 0644 root root # 不压缩 nocompress # 备份日志文件但是不截断 nocopytruncate # 如果是空文件的话,不转储 notifempty # 如果日志丢失,不报错继续滚动下一个日志 missingok # 转储后的日志文件和当前日志文件放在同一个目录下 noolddir # 使用当期日期作为命名格式 dateext # 指定日志文件删除之前转储的个数,5指保留5个备份 rotate 10 # 当日志文件到达指定的大小时才转储 size=100MB- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21

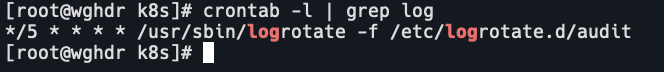
创建crontab
*/5 * * * * /usr/sbin/logrotate -f /etc/logrotate.d/audit- 1
查看轮转
ll /var/log/k8s/- 1

-
相关阅读:
ISP代理是什么?双ISP是什么意思?
Shrio整合Jwt
记录7种常见字符编码
数据结构第一篇【探究List和ArrayList之间的奥秘 】
云端golang开发,无需本地配置,能上网就能开发和运行
【基于TCP 在线电子词典】
即刻报名,企业服务与新经济论坛亮点提前揭秘!
“碳”零排放是什么意思
基于单片机的线路差动保护系统设计
一种通过nacos动态配置实现多租户的log4j2日志物理隔离的设计
- 原文地址:https://blog.csdn.net/weixin_43616190/article/details/126433538
