-
(2022版)一套教程搞定k8s安装到实战 | K8s集群安装(二进制)
视频来源:B站《(2022版)最新、最全、最详细的Kubernetes(K8s)教程,从K8s安装到实战一套搞定》
一边学习一边整理老师的课程内容及试验笔记,并与大家分享,侵权即删,谢谢支持!
附上汇总贴:(2022版)一套教程搞定k8s安装到实战 | 汇总_COCOgsta的博客-CSDN博客
基本环境配置
主机信息,服务器IP地址不能设置为dhcp,要配置静态IP。
VIP(虚拟IP)不要和公司内网IP重复,首先去ping一下,不通才可用。VIP需要和主机在同一个局域网内!
- 192.168.1.107 k8s-master01 # 2C2G 20G
- 192.168.1.108 k8s-master02 # 2C2G 20G
- 192.168.1.109 k8s-master03 # 2C2G 20G
- 192.168.1.236 k8s-master-lb # VIP虚IP不占用机器资源 # 如果不是高可用集群,该IP为Master01的IP
- 192.168.1.110 k8s-node01 # 2C2G 20G
- 192.168.1.111 k8s-node02 # 2C2G 20G
K8s Service网段:10.96.0.0/12
K8s Pod网段:172.16.0.0/12
系统环境:
- [root@master01 ~]# cat /etc/redhat-release
- CentOS Linux release 7.9.2009 (Core)
- [root@master01 ~]#
虚拟机环境:


配置所有节点hosts文件
- [root@master01 ~]# cat /etc/hosts
- 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
- ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
- 192.168.1.107 k8s-master01
- 192.168.1.108 k8s-master02
- 192.168.1.109 k8s-master03
- 192.168.1.236 k8s-master-lb
- 192.168.1.110 k8s-node01
- 192.168.1.111 k8s-node02
- [root@master01 ~]#
CentOS7安装yum源如下:
- curl -o /etc/yum.repos.d/CentOS-Base.repo https://mirrors.aliyun.com/repo/Centos-7.repo
- yum install -y yum-utils device-mapper-persistent-data lvm2
- yum-config-manager --add-repo https://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
- sed -i -e '/mirrors.cloud.aliyuncs.com/d' -e '/mirrors.aliyuncs.com/d' /etc/yum.repos.d/CentOS-Base.repo
必备工具安装
yum install wget jq psmisc vim net-tools telnet yum-utils device-mapper-persistent-data lvm2 git -y所有节点关闭firewalld、dnsmasq、selinux
- systemctl disable --now firewalld
- systemctl disable --now dnsmasq
- setenforce 0
- sed -i 's#SELINUX=enforcing#SELINUX=disabled#g' /etc/sysconfig/selinux
- sed -i 's#SELINUX=enforcing#SELINUX=disabled#g' /etc/selinux/config
所有节点关闭swap分区,fstab注释swap
- swapoff -a && sysctl -w vm.swappiness=0
- sed -ri '/^[^#]*swap/s@^@#@' /etc/fstab
所有节点同步时间
安装ntpdate
- rpm -ivh http://mirrors.wlnmp.com/centos/wlnmp-release-centos.noarch.rpm
- yum install ntpdate -y
所有节点同步时间。时间同步配置如下:
- ln -sf /usr/share/zoneinfo/Asia/Shanghai /etc/localtime
- echo 'Asia/Shanghai' > /etc/timezone
- ntpdate time2.aliyun.com
- # 加入到crontab
- crontab -e
- */5 * * * * ntpdate time2.aliyun.com
所有节点配置limit:
- ulimit -SHn 65535
- vim /etc/security/limits.conf
- #末尾添加如下内容
- * soft nofile 655360
- * hard nofile 131072
- * soft nproc 655350
- * hard nproc 655350
- * soft memlock unlimited
- * hard memlock unlimited
Master01节点免密钥登录其他节点,安装过程中生成配置文件和证书均在Master01上操作,集群管理也在Master01上操作,阿里云或者AWS上需要单独一台kubectl服务器。密钥配置如下:
[root@k8s-master01 ~]# ssh-keygen -t rsaMaster01配置免密码登录其他节点
for i in k8s-master01 k8s-master02 k8s-master03 k8s-node01 k8s-node02;do ssh-copy-id -i .ssh/id_rsa.pub $i;doneMaster01下载安装文件
- git config --global --unset http.proxy
- git config --global --unset https.proxy
- git clone https://github.com/dotbalo/k8s-ha-install.git
所有节点升级系统并重启,此处升级没有升级内核,升级内核可参考之前的内容一套教程搞定k8s安装到实战 。
yum update -y --exclude=kernel* --skip-broken && reboot #CentOS需要升级,CentOS8可以按需升级系统基本组件安装
本节主要安装的是集群中用到各种组件,比如Docker-ce、Kubernetes各组件等。
Docker安装
所有节点安装Docker-ce 19.03
yum install docker-ce-19.03.* -y温馨提示:
由于新版kubelet建议使用systemd,所以可以把docker的CgroupDriver改成systemd
- mkdir /etc/docker
- cat > /etc/docker/daemon.json <<EOF
- {
- "exec-opts":["native.cgroupdriver=systemd"]
- }
- EOF
所有节点设置开机自启动Docker:
systemctl daemon-reload && systemctl enable --now dockerK8s及etcd安装
Master01下载kubernetes安装包
wget https://dl.k8s.io/v1.20.0/kubernetes-server-linux-amd64.tar.gz下载etcd安装包
wget https://github.com/etcd-io/etcd/releases/download/v3.4.13/etcd-v3.4.13-linux-amd64.tar.gz解压kubernetes安装文件
tar -xf kubernetes-server-linux-amd64.tar.gz --strip-components=3 -C /usr/local/bin kubernetes/server/bin/kube{let,ctl,-apiserver,-controller-manager,-scheduler,-proxy}解压etcd安装文件
tar -zxvf etcd-v3.4.13-linux-amd64.tar.gz --strip-components=1 -C /usr/local/bin etcd-v3.4.13-linux-amd64/etcd{,ctl}版本查看
- [root@k8s-master01 ~]# kubelet --version
- Kubernetes v1.20.0
- [root@k8s-master01 ~]#
- [root@k8s-master01 ~]# etcdctl version
- etcdctl version: 3.4.13
- API version: 3.4
- [root@k8s-master01 ~]#
将组件发送到其他节点
- MasterNodes='k8s-master02 k8s-master03'
- WorkNodes='k8s-node01 k8s-node02'
- for NODE in $MasterNodes;do echo $NODE;scp /usr/local/bin/kube{let,ctl,-apiserver,-controller-manager,-scheduler,-proxy} $NODE:/usr/local/bin/;scp /usr/local/bin/etcd* $NODE:/usr/local/bin;done
- for NODE in $WorkNodes;do scp /usr/local/bin/kube{let,-proxy} $NODE:/usr/local/bin;done
所有节点创建/opt/cni/bin目录
mkdir -p /opt/cni/bin切换分支
- git branch -a
- git checkout manual-installation-v1.20.x
生成证书
二进制安装最关键步骤,一步错误全盘皆输,一定要注意每个步骤都要是正确的
Master01下载生成证书工具
- wget "https://pkg.cfssl.org/R1.2/cfssl_linux-amd64" -O /usr/local/bin/cfssl
- wget "https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64" -O /usr/local/bin/cfssljson
- chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson
所有Master节点创建etcd证书目录
mkdir /etc/etcd/ssl -p所有节点创建kubernetes相关目录
mkdir -p /etc/kubernetes/pkiMaster01节点生成etcd证书
生成证书的CSR文件:证书签名请求文件,配置了一些域名、公司、单位
- cd /root/k8s-ha-install/pki
- # 生成CA证书和CA证书的key
- cfssl gencert -initca etcd-ca-csr.json | cfssljson -bare /etc/etcd/ssl/etcd-ca
- # 曾在这里因为hostname问题导致etcd服务无法启动,后删除无用的ip地址,并修改节点域名为IP地址解决
- cfssl gencert -ca=/etc/etcd/ssl/etcd-ca.pem -ca-key=/etc/etcd/ssl/etcd-ca-key.pem -config=ca-config.json -hostname=127.0.0.1,192.168.1.107,192.168.1.108,192.168.1.109 -profile=kubernetes etcd-csr.json|cfssljson -bare /etc/etcd/ssl/etcd
将证书复制到其他节点
- MasterNodes='k8s-master02 k8s-master03'
- WorkNodes='k8s-node01 k8s-node02'
- for NODE in $MasterNodes;do
- ssh $NODE "mkdir -p /etc/etcd/ssl"
- for FILE in etcd-ca-key.pem etcd-ca.pem etcd-key.pem etcd.pem;do
- scp /etc/etcd/ssl/${FILE} $NODE:/etc/etcd/ssl/${FILE}
- done
- done
Master01生成kubernetes证书
- cfssl gencert -initca ca-csr.json | cfssljson -bare /etc/kubernetes/pki/ca
- # 10.96.0是k8s service的网段,如果说需要更改k8s service网段,那就需要更改10.96.0.1
- cfssl gencert -ca=/etc/kubernetes/pki/ca.pem -ca-key=/etc/kubernetes/pki/ca-key.pem -config=ca-config.json -hostname=10.96.0.1,192.168.1.236,127.0.0.1,kubernetes,kubernetes.default.svc,kubernetes.default.svc.cluster,kubernetes.default.svc.cluster.local,192.168.1.107,192.168.1.108,192.168.1.109 -profile=kubernetes apiserver-csr.json|cfssljson -bare /etc/kubernetes/pki/apiserver
- cfssl gencert -initca front-proxy-ca-csr.json|cfssljson -bare /etc/kubernetes/pki/front-proxy-ca
- # 生成apiserver的聚合证书。Requestheader-client-xxx request-allowed-xxx:aggregator
- cfssl gencert -ca=/etc/kubernetes/pki/front-proxy-ca.pem -ca-key=/etc/kubernetes/pki/front-proxy-ca-key.pem -config=ca-config.json -profile=kubernetes front-proxy-client-csr.json|cfssljson -bare /etc/kubernetes/pki/front-proxy-client
- # 生成controller-manage的证书
- cfssl gencert -ca=/etc/kubernetes/pki/ca.pem -ca-key=/etc/kubernetes/pki/ca-key.pem -config=ca-config.json -profile=kubernetes manager-csr.json|cfssljson -bare /etc/kubernetes/pki/controller-manager
- # set-cluster:设置一个集群项
- kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.pem --embed-certs=true --server=https://192.168.1.236:8443 --kubeconfig=/etc/kubernetes/controller-manager.kubeconfig
- # 设置一个环境项,一个上下文
- kubectl config set-context system:kube-controller-manager@kubernetes --cluster=kubernetes --user=system:kube-controller-manager --kubeconfig=/etc/kubernetes/controller-manager.kubeconfig
- # set-credentials 设置一个用户项
- kubectl config set-credentials system:kube-controller-manager --client-certificate=/etc/kubernetes/pki/controller-manager.pem --client-key=/etc/kubernetes/pki/controller-manager-key.pem --embed-certs=true --kubeconfig=/etc/kubernetes/controller-manager.kubeconfig
- #使用某个环境当做默认环境
- kubectl config use-context system:kube-controller-manager@kubernetes --kubeconfig=/etc/kubernetes/controller-manager.kubeconfig
- cfssl gencert -ca=/etc/kubernetes/pki/ca.pem -ca-key=/etc/kubernetes/pki/ca-key.pem -config=ca-config.json -profile=kubernetes scheduler-csr.json | cfssljson -bare /etc/kubernetes/pki/scheduler
- kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.pem --embed-certs=true --server=https://192.168.1.236:8443 --kubeconfig=/etc/kubernetes/scheduler.kubeconfig
- kubectl config set-credentials system:kube-scheduler --client-certificate=/etc/kubernetes/pki/scheduler.pem --client-key=/etc/kubernetes/pki/scheduler-key.pem --embed-certs=true --kubeconfig=/etc/kubernetes/scheduler.kubeconfig
- kubectl config set-context system:kube-scheduler@kubernetes --cluster=kubernetes --user=system:kube-scheduler --kubeconfig=/etc/kubernetes/scheduler.kubeconfig
- kubectl config use-context system:kube-scheduler@kubernetes --kubeconfig=/etc/kubernetes/scheduler.kubeconfig
- cfssl gencert -ca=/etc/kubernetes/pki/ca.pem -ca-key=/etc/kubernetes/pki/ca-key.pem -config=ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare /etc/kubernetes/pki/admin
- kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.pem --embed-certs=true --server=https://192.168.1.236:8443 --kubeconfig=/etc/kubernetes/admin.kubeconfig
- kubectl config set-credentials kubernetes-admin --client-certificate=/etc/kubernetes/pki/admin.pem --client-key=/etc/kubernetes/pki/admin-key.pem --embed-certs=true --kubeconfig=/etc/kubernetes/admin.kubeconfig
- kubectl config set-context kubernetes-admin@kubernetes --cluster=kubernetes --user=kubernetes-admin --kubeconfig=/etc/kubernetes/admin.kubeconfig
- kubectl config use-context kubernetes-admin@kubernetes --kubeconfig=/etc/kubernetes/admin.kubeconfig
创建ServiceAccount Key
- openssl genrsa -out /etc/kubernetes/pki/sa.key 2048
- openssl rsa -in /etc/kubernetes/pki/sa.key -pubout -out /etc/kubernetes/pki/sa.pub
- for NODE in k8s-master02 k8s-master03;do
- for FILE in $(ls /etc/kubernetes/pki | grep -v etcd);do
- scp /etc/kubernetes/pki/${FILE} $NODE:/etc/kubernetes/pki/${FILE};
- done;
- for FILE in admin.kubeconfig controller-manager.kubeconfig scheduler.kubeconfig;do
- scp /etc/kubernetes/${FILE} $NODE:/etc/kubernetes/${FILE};
- done;
- done
- # 确认生成的文件有23个
- [root@k8s-master01 pki]# ls /etc/kubernetes/pki | wc -l
- 23
- [root@k8s-master01 pki]#
Kubernetes系统组件配置
etcd配置
etcd配置大致相同,注意修改每个Master节点的etcd配置的主机名和IP地址
Master01
- vim /etc/etcd/etcd.config.yml
- name: 'k8s-master01'
- data-dir: /var/lib/etcd
- wal-dir: /var/lib/etcd/wal
- snapshot-count: 5000
- heartbeat-interval: 100
- election-timeout: 1000
- quota-backend-bytes: 0
- listen-peer-urls: 'https://192.168.1.107:2380'
- listen-client-urls: 'https://192.168.1.107:2379,http://127.0.0.1:2379'
- max-snapshots: 3
- max-wals: 5
- cors:
- initial-advertise-peer-urls: 'https://192.168.1.107:2380'
- advertise-client-urls: 'https://192.168.0.107:2379'
- discovery:
- discovery-fallback: 'proxy'
- discovery-proxy:
- discovery-srv:
- initial-cluster: 'k8s-master01=https://192.168.1.107:2380,k8s-master02=https://192.168.1.108:2380,k8s-master03=https://192.168.1.109:2380'
- initial-cluster-token: 'etcd-k8s-cluster'
- initial-cluster-state: 'new'
- strict-reconfig-check: false
- enable-v2: true
- enable-pprof: true
- proxy: 'off'
- proxy-failure-wait: 5000
- proxy-refresh-interval: 30000
- proxy-dial-timeout: 1000
- proxy-write-timeout: 0
- client-transport-security:
- cert-file: '/etc/kubernetes/pki/etcd/etcd.pem'
- key-file: 'etc/kubernetes/pki/etcd/etcd-key.pem'
- client-cert-auth: true
- trusted-ca-file: '/etc/kubernetes/pki/etcd/etcd-ca.pem'
- auto-tls: true
- peer-transport-security:
- cert-file: '/etc/kubernetes/pki/etcd/etcd.pem'
- key-file: '/etc/kubernetes/pki/etcd/etcd-key.pem'
- peer-client-cert-auth: true
- trusted-ca-file: '/etc/kubernetes/pki/etcd/etcd-ca.pem'
- auto-tls: true
- debug: false
- log-package-levels:
- log-outputs: [default]
- force-new-cluster: false
Master02
- vim /etc/etcd/etcd.config.yml
- name: 'k8s-master02'
- data-dir: /var/lib/etcd
- wal-dir: /var/lib/etcd/wal
- snapshot-count: 5000
- heartbeat-interval: 100
- election-timeout: 1000
- quota-backend-bytes: 0
- listen-peer-urls: 'https://192.168.1.108:2380'
- listen-client-urls: 'https://192.168.1.108:2379,http://127.0.0.1:2379'
- max-snapshots: 3
- max-wals: 5
- cors:
- initial-advertise-peer-urls: 'https://192.168.1.108:2380'
- advertise-client-urls: 'https://192.168.1.108:2379'
- discovery:
- discovery-fallback: 'proxy'
- discovery-proxy:
- discovery-srv:
- initial-cluster: 'k8s-master01=https://192.168.1.107:2380,k8s-master02=https://192.168.1.108:2380,k8s-master03=https://192.168.1.109:2380'
- initial-cluster-token: 'etcd-k8s-cluster'
- initial-cluster-state: 'new'
- strict-reconfig-check: false
- enable-v2: true
- enable-pprof: true
- proxy: 'off'
- proxy-failure-wait: 5000
- proxy-refresh-interval: 30000
- proxy-dial-timeout: 1000
- proxy-write-timeout: 0
- client-transport-security:
- cert-file: '/etc/kubernetes/pki/etcd/etcd.pem'
- key-file: '/etc/kubernetes/pki/etcd/etcd-key.pem'
- client-cert-auth: true
- trusted-ca-file: '/etc/kubernetes/pki/etcd/etcd-ca.pem'
- auto-tls: true
- peer-transport-security:
- cert-file: '/etc/kubernetes/pki/etcd/etcd.pem'
- key-file: '/etc/kubernetes/pki/etcd/etcd-key.pem'
- peer-client-cert-auth: true
- trusted-ca-file: '/etc/kubernetes/pki/etcd/etcd-ca.pem'
- auto-tls: true
- debug: false
- log-package-levels:
- log-outputs: [default]
- force-new-cluster: false
Master03
- vim /etc/etcd/etcd.config.yml
- name: 'k8s-master03'
- data-dir: /var/lib/etcd
- wal-dir: /var/lib/etcd/wal
- snapshot-count: 5000
- heartbeat-interval: 100
- election-timeout: 1000
- quota-backend-bytes: 0
- listen-peer-urls: 'https://192.168.1.109:2380'
- listen-client-urls: 'https://192.168.1.109:2379,http://127.0.0.1:2379'
- max-snapshots: 3
- max-wals: 5
- cors:
- initial-advertise-peer-urls: 'https://192.168.1.109:2380'
- advertise-client-urls: 'https://192.168.1.109:2379'
- discovery:
- discovery-fallback: 'proxy'
- discovery-proxy:
- discovery-srv:
- initial-cluster: 'k8s-master01=https://192.168.1.107:2380,k8s-master02=https://192.168.1.108:2380,k8s-master03=https://192.168.1.109:2380'
- initial-cluster-token: 'etcd-k8s-cluster'
- initial-cluster-state: 'new'
- strict-reconfig-check: false
- enable-v2: true
- enable-pprof: true
- proxy: 'off'
- proxy-failure-wait: 5000
- proxy-refresh-interval: 30000
- proxy-dial-timeout: 1000
- proxy-write-timeout: 0
- client-transport-security:
- cert-file: '/etc/kubernetes/pki/etcd/etcd.pem'
- key-file: '/etc/kubernetes/pki/etcd/etcd-key.pem'
- client-cert-auth: true
- trusted-ca-file: '/etc/kubernetes/pki/etcd/etcd-ca.pem'
- auto-tls: true
- peer-transport-security:
- cert-file: '/etc/kubernetes/pki/etcd/etcd.pem'
- key-file: '/etc/kubernetes/pki/etcd/etcd-key.pem'
- peer-client-cert-auth: true
- trusted-ca-file: '/etc/kubernetes/pki/etcd/etcd-ca.pem'
- auto-tls: true
- debug: false
- log-package-levels:
- log-outputs: [default]
- force-new-cluster: false
创建Service
所有Master节点创建etcd service并启动
- vi /usr/lib/systemd/system/etcd.service
- [Unit]
- Description=Etcd Service
- Documentation=https://coreos.com/etcd/docs/latest/
- After=network.target
- [Service]
- Type=notify
- ExecStart=/usr/local/bin/etcd --config-file=/etc/etcd/etcd.config.yml
- Restart=on-failure
- RestartSec=10
- LimitNOFILE=65536
- [Install]
- WantedBy=multi-user.target
- Alias=etcd3.service
所有Master节点创建etcd的证书目录
- mkdir /etc/kubernetes/pki/etcd
- ln -s /etc/etcd/ssl/* /etc/kubernetes/pki/etcd
- systemctl daemon-reload
- systemctl enable --now etcd
查看etcd状态
- [root@k8s-master01 etcd]# export ETCDCTL_API=3
- [root@k8s-master01 pki]# etcdctl --endpoints="192.168.1.109:2379,192.168.1.108:2379,192.168.1.107:2379" --cacert=/etc/kubernetes/pki/etcd/etcd-ca.pem --cert=/etc/kubernetes/pki/etcd/etcd.pem --key=/etc/kubernetes/pki/etcd/etcd-key.pem endpoint status --write-out=table
- +--------------------+------------------+---------+---------+-----------+------------+-----------+------------+--------------------+--------+
- | ENDPOINT | ID | VERSION | DB SIZE | IS LEADER | IS LEARNER | RAFT TERM | RAFT INDEX | RAFT APPLIED INDEX | ERRORS |
- +--------------------+------------------+---------+---------+-----------+------------+-----------+------------+--------------------+--------+
- | 192.168.1.109:2379 | 40ebe70dffb00505 | 3.4.13 | 20 kB | false | false | 14 | 9 | 9 | |
- | 192.168.1.108:2379 | 4087302bf9046cf1 | 3.4.13 | 20 kB | false | false | 14 | 9 | 9 | |
- | 192.168.1.107:2379 | 8af8195104313994 | 3.4.13 | 20 kB | true | false | 14 | 9 | 9 | |
- +--------------------+------------------+---------+---------+-----------+------------+-----------+------------+--------------------+--------+
- [root@k8s-master01 pki]#
高可用配置
高可用配置(注意:如果不是高可用集群,haproxy和keepalived无需安装)
如果在云上安装也无需执行此章节的步骤,可以直接使用云上的lb,比如阿里云slb,腾讯云elb等
所有Master节点安装keepalived和haproxy
yum install keepalived haproxy -y所有Master配置HAProxy,配置一样
- vi /etc/haproxy/haproxy.cfg
- global
- maxconn 2000
- ulimit-n 16384
- log 127.0.0.1 local0 err
- stats timeout 30s
- defaults
- log global
- mode http
- option httplog
- timeout connect 5000
- timeout client 50000
- timeout server 50000
- timeout http-request 15s
- timeout http-keep-alive 15s
- frontend k8s-master
- bind 0.0.0.0:8443
- bind 127.0.0.1:8443
- mode tcp
- option tcplog
- tcp-request inspect-delay 5s
- default_backend k8s-master
- backend k8s-master
- mode tcp
- option tcplog
- option tcp-check
- balance roundrobin
- default-server inter 10s downinter 5s rise 2 fall 2 slowstart 60s maxconn 250 maxqueue 256 weight 100
- server k8s-master01 192.168.1.107:6443 check
- server k8s-master02 192.168.1.108:6443 check
- server k8s-master03 192.168.1.109:6443 check
Master01 keepalived
所有Master节点配置KeepAlived,配置不一样,注意区分[root@k8s-master01 pki]# vim
/etc/keepalived/keepalived.conf,注意每个节点的IP和网卡(interface参数)- !Configuration File for keepalived
- global_defs {
- router_id LVS_DEVEL
- }
- vrrp_script chk_apiserver {
- script "/etc/keepalived/check_apiserver.sh"
- interval 5
- weight -5
- fall 2
- rise 1
- }
- vrrp_instance VI_1 {
- state MASTER
- interface eno16777736
- mcast_src_ip 192.168.1.107
- virtual_router_id 51
- priority 101
- nopreempt
- advert_int 2
- authentication {
- auth_type PASS
- auth_pass K8SHA_KA_AUTH
- }
- virtual_ipaddress {
- 192.168.1.236
- }
- track_script {
- chk_apiserver
- }
- }
Master02 keepalived
- !Configuration File for keepalived
- global_defs {
- router_id LVS_DEVEL
- }
- vrrp_script chk_apiserver {
- script "/etc/keepalived/check_apiserver.sh"
- interval 5
- weight -5
- fall 2
- rise 1
- }
- vrrp_instance VI_1 {
- state BACKUP
- interface eno16777736
- mcast_src_ip 192.168.1.108
- virtual_router_id 51
- priority 100
- nopreempt
- advert_int 2
- authentication {
- auth_type PASS
- auth_pass K8SHA_KA_AUTH
- }
- virtual_ipaddress {
- 192.168.1.236
- }
- track_script {
- chk_apiserver
- }
- }
Master03 keepalived
- !Configuration File for keepalived
- global_defs {
- router_id LVS_DEVEL
- }
- vrrp_script chk_apiserver {
- script "/etc/keepalived/check_apiserver.sh"
- interval 5
- weight -5
- fall 2
- rise 1
- }
- vrrp_instance VI_1 {
- state BACKUP
- interface eno16777736
- mcast_src_ip 192.168.1.109
- virtual_router_id 51
- priority 100
- nopreempt
- advert_int 2
- authentication {
- auth_type PASS
- auth_pass K8SHA_KA_AUTH
- }
- virtual_ipaddress {
- 192.168.1.236
- }
- track_script {
- chk_apiserver
- }
- }
健康检查配置
所有master节点
- vi /etc/keepalived/check_apiserver.sh
- #!/bin/bash
- err=0
- for k in $(seq 1 3)
- do
- check_code=$(pgrep haproxy)
- if [[ $check_code == "" ]]; then
- err=$(expr $err +1)
- sleep 1
- continue
- else
- err=0
- break
- fi
- done
- if [[ $err != "0" ]]; then
- echo "systemctl stop keepalived"
- /usr/bin/systemctl stop keepalived
- exit 1
- else
- exit 0
- fi
chmod +x /etc/keepalived/check_apiserver.sh所有master节点启动haproxy和keepalived
- systemctl daemon-reload
- systemctl enable --now haproxy
- systemctl enable --now keepalived
VIP测试
- [root@k8s-master01 pki]# ping 192.168.1.236
- PING 192.168.1.236 (192.168.1.236) 56(84) bytes of data.
- 64 bytes from 192.168.1.236: icmp_seq=1 ttl=64 time=0.033 ms
- 64 bytes from 192.168.1.236: icmp_seq=2 ttl=64 time=0.081 ms
- 64 bytes from 192.168.1.236: icmp_seq=3 ttl=64 time=0.077 ms
- ^C
- --- 192.168.1.236 ping statistics ---
- 3 packets transmitted, 3 received, 0% packet loss, time 2042ms
- rtt min/avg/max/mdev = 0.033/0.063/0.081/0.023 ms
- [root@k8s-master01 pki]#
重要:如果安装了keepalived和haproxy, 需要测试keepalived是否是正常的
- [root@k8s-master01 pki]# telnet 192.168.1.236 8443
- Trying 192.168.1.236...
- Connected to 192.168.1.236.
- Escape character is '^]'.
- Connection closed by foreign host.
- [root@k8s-master01 pki]#
如果ping不通且telnet没有出现']',则认为VIP不可以,不可再继续往下执行,需要排查keepalived的问题,比如防火墙和selinux,haproxy和keepalived的状态,监听端口灯
所有节点查看防火墙状态必须为disable和inactive:systemctl status firewalld
所有节点查看selinux状态,必须为disable:getenforce
master节点查看haproxy和keepalived状态:systemctl status keepalived haproxy
Kubernetes系统组件配置(续)
Apiserver
所有节点创建相关目录
mkdir -p /etc/kubernetes/manifest/ /etc/systemd/system/kubelet.service.d /var/lib/kubelet /var/log/kubernetes所有Master节点创建kube-apiserver service,# 注意,如果不是高可用集群,192.168.1.236改为master01的地址
Master01配置
注意本文档使用的k8s service网段为10.96.0.0/12,该网段不能和宿主机的网段、Pod网段重复,请按需修改
- vi /usr/lib/systemd/system/kube-apiserver.service
- [Unit]
- Description=Kubernetes API Server
- Documentation=https://github.com/kubernetes/kubernetes
- After=network.target
- [Service]
- ExecStart=/usr/local/bin/kube-apiserver \
- --v=2 \
- --logtostderr=true \
- --allow-privileged=true \
- --bind-address=0.0.0.0 \
- --secure-port=6443 \
- --insecure-port=0 \
- --advertise-address=192.168.1.107 \
- --service-cluster-ip-range=10.96.0.0/12 \
- --service-node-port-range=30000-32767 \
- --etcd-servers=https://192.168.1.107:2379,https://192.168.1.108:2379,https://192.168.1.109:2379 \
- --etcd-cafile=/etc/etcd/ssl/etcd-ca.pem \
- --etcd-certfile=/etc/etcd/ssl/etcd.pem \
- --etcd-keyfile=/etc/etcd/ssl/etcd-key.pem \
- --client-ca-file=/etc/kubernetes/pki/ca.pem \
- --tls-cert-file=/etc/kubernetes/pki/apiserver.pem \
- --tls-private-key-file=/etc/kubernetes/pki/apiserver-key.pem \
- --kubelet-client-certificate=/etc/kubernetes/pki/apiserver.pem \
- --kubelet-client-key=/etc/kubernetes/pki/apiserver-key.pem \
- --service-account-key-file=/etc/kubernetes/pki/sa.pub \
- --service-account-signing-key-file=/etc/kubernetes/pki/sa.key \
- --service-account-issuer=https://kubernetes.default.svc.cluster.local \
- --kubelet-preferred-address-types=InternalIP,ExternalIP,Hostname \
- --enable-admission-plugins=NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,DefaultTolerationSeconds,NodeRestriction,ResourceQuota \
- --authorization-mode=Node,RBAC \
- --enable-bootstrap-token-auth=true \
- --requestheader-client-ca-file=/etc/kubernetes/pki/front-proxy-ca.pem \
- --proxy-client-cert-file=/etc/kubernetes/pki/front-proxy-client.pem \
- --proxy-client-key-file=/etc/kubernetes/pki/front-proxy-client-key.pem \
- --requestheader-allowed-names=aggregator \
- --requestheader-extra-headers-prefix=X-Remote-Group \
- --requestheader-username-headers=X-Remote-User
- # --token-auth-file=/etc/kubernetes/token.csv
- Restart=on-failure
- RestartSec=10s
- LimitNOFILE=65535
- [Install]
- WantedBy=multi-user.target
Master02配置
- vi /usr/lib/systemd/system/kube-apiserver.service
- [Unit]
- Description=Kubernetes API Server
- Documentation=https://github.com/kubernetes/kubernetes
- After=network.target
- [Service]
- ExecStart=/usr/local/bin/kube-apiserver \
- --v=2 \
- --logtostderr=true \
- --allow-privileged=true \
- --bind-address=0.0.0.0 \
- --secure-port=6443 \
- --insecure-port=0 \
- --advertise-address=192.168.1.108 \
- --service-cluster-ip-range=10.96.0.0/12 \
- --service-node-port-range=30000-32767 \
- --etcd-servers=https://192.168.1.107:2379,https://192.168.1.108:2379,https://192.168.1.109:2379 \
- --etcd-cafile=/etc/etcd/ssl/etcd-ca.pem \
- --etcd-certfile=/etc/etcd/ssl/etcd.pem \
- --etcd-keyfile=/etc/etcd/ssl/etcd-key.pem \
- --client-ca-file=/etc/kubernetes/pki/ca.pem \
- --tls-cert-file=/etc/kubernetes/pki/apiserver.pem \
- --tls-private-key-file=/etc/kubernetes/pki/apiserver-key.pem \
- --kubelet-client-certificate=/etc/kubernetes/pki/apiserver.pem \
- --kubelet-client-key=/etc/kubernetes/pki/apiserver-key.pem \
- --service-account-key-file=/etc/kubernetes/pki/sa.pub \
- --service-account-signing-key-file=/etc/kubernetes/pki/sa.key \
- --service-account-issuer=https://kubernetes.default.svc.cluster.local \
- --kubelet-preferred-address-types=InternalIP,ExternalIP,Hostname \
- --enable-admission-plugins=NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,DefaultTolerationSeconds,NodeRestriction,ResourceQuota \
- --authorization-mode=Node,RBAC \
- --enable-bootstrap-token-auth=true \
- --requestheader-client-ca-file=/etc/kubernetes/pki/front-proxy-ca.pem \
- --proxy-client-cert-file=/etc/kubernetes/pki/front-proxy-client.pem \
- --proxy-client-key-file=/etc/kubernetes/pki/front-proxy-client-key.pem \
- --requestheader-allowed-names=aggregator \
- --requestheader-group-headers=X-Remote-Group \
- --requestheader-extra-headers-prefix=X-Remote-Extra- \
- --requestheader-username-headers=X-Remote-User
- # --token-auth-file=/etc/kubernetes/token.csv
- Restart=on-failure
- RestartSec=10s
- LimitNOFILE=65535
- [Install]
- WantedBy=multi-user.target
Master03配置
- vi /usr/lib/systemd/system/kube-apiserver.service
- [Unit]
- Description=Kubernetes API Server
- Documentation=https://github.com/kubernetes/kubernetes
- After=network.target
- [Service]
- ExecStart=/usr/local/bin/kube-apiserver \
- --v=2 \
- --logtostderr=true \
- --allow-privileged=true \
- --bind-address=0.0.0.0 \
- --secure-port=6443 \
- --insecure-port=0 \
- --advertise-address=192.168.1.109 \
- --service-cluster-ip-range=10.96.0.0/12 \
- --service-node-port-range=30000-32767 \
- --etcd-servers=https://192.168.1.107:2379,https://192.168.1.108:2379,https://192.168.1.109:2379 \
- --etcd-cafile=/etc/etcd/ssl/etcd-ca.pem \
- --etcd-certfile=/etc/etcd/ssl/etcd.pem \
- --etcd-keyfile=/etc/etcd/ssl/etcd-key.pem \
- --client-ca-file=/etc/kubernetes/pki/ca.pem \
- --tls-cert-file=/etc/kubernetes/pki/apiserver.pem \
- --tls-private-key-file=/etc/kubernetes/pki/apiserver-key.pem \
- --kubelet-client-certificate=/etc/kubernetes/pki/apiserver.pem \
- --kubelet-client-key=/etc/kubernetes/pki/apiserver-key.pem \
- --service-account-key-file=/etc/kubernetes/pki/sa.pub \
- --service-account-signing-key-file=/etc/kubernetes/pki/sa.key \
- --service-account-issuer=https://kubernetes.default.svc.cluster.local \
- --kubelet-preferred-address-types=InternalIP,ExternalIP,Hostname \
- --enable-admission-plugins=NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,DefaultTolerationSeconds,NodeRestriction,ResourceQuota \
- --authorization-mode=Node,RBAC \
- --enable-bootstrap-token-auth=true \
- --requestheader-client-ca-file=/etc/kubernetes/pki/front-proxy-ca.pem \
- --proxy-client-cert-file=/etc/kubernetes/pki/front-proxy-client.pem \
- --proxy-client-key-file=/etc/kubernetes/pki/front-proxy-client-key.pem \
- --requestheader-allowed-names=aggregator \
- --requestheader-group-headers=X-Remote-Group \
- --requestheader-extra-headers-prefix=X-Remote-Extra- \
- --requestheader-username-headers=X-Remote-User
- # --token-auth-file=/etc/kubernetes/token.csv
- Restart=on-failure
- RestartSec=10s
- LimitNOFILE=65535
- [Install]
- WantedBy=multi-user.target
启动apiserver
所有Master节点开启kube-apiserver
systemctl daemon-reload && systemctl enable --now kube-apiserver检测kube-server状态
- [root@k8s-master01 pki]# systemctl status kube-apiserver
- ● kube-apiserver.service - Kubernetes API Server
- Loaded: loaded (/usr/lib/systemd/system/kube-apiserver.service; enabled; vendor preset: disabled)
- Active: active (running) since Tue 2022-06-21 21:15:19 CST; 11s ago
- Docs: https://github.com/kubernetes/kubernetes
- Main PID: 4604 (kube-apiserver)
- Tasks: 8
- Memory: 276.4M
- CGroup: /system.slice/kube-apiserver.service
- └─4604 /usr/local/bin/kube-apiserver --v=2 --logtostderr=true --allow-privileged=true --bind-address=0.0.0.0 --secure-port=6443 --insecure-port=0 --advertise-address=192.168.1.107 --serv...
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: [-]poststarthook/rbac/bootstrap-roles failed: not finished
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: I0621 21:15:25.359623 4604 healthz.go:244] poststarthook/rbac/bootstrap-roles check failed: readyz
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: [-]poststarthook/rbac/bootstrap-roles failed: not finished
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: I0621 21:15:25.457019 4604 healthz.go:244] poststarthook/rbac/bootstrap-roles check failed: readyz
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: [-]poststarthook/rbac/bootstrap-roles failed: not finished
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: I0621 21:15:25.557168 4604 healthz.go:244] poststarthook/rbac/bootstrap-roles check failed: readyz
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: [-]poststarthook/rbac/bootstrap-roles failed: not finished
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: W0621 21:15:25.714977 4604 lease.go:233] Resetting endpoints for master service "kubernetes" to [192.168.1.107 192.168.1.108 192.168.1.109]
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: I0621 21:15:25.718182 4604 controller.go:606] quota admission added evaluator for: endpoints
- Jun 21 21:15:25 k8s-master-lb kube-apiserver[4604]: I0621 21:15:25.726940 4604 controller.go:606] quota admission added evaluator for: endpointslices.discovery.k8s.io
- [root@k8s-master01 pki]#
ControllerManager
所有Master节点配置kube-controller-manager service
- vi /usr/lib/systemd/system/kube-controller-manager.service
- [Unit]
- Description=Kubernetes Controller Manager
- Documentation=https://github.com/kubernetes/kubernetes
- After=network.target
- [Service]
- ExecStart=/usr/local/bin/kube-controller-manager \
- --v=2 \
- --logtostderr=true \
- --address=127.0.0.1 \
- --root-ca-file=/etc/kubernetes/pki/ca.pem \
- --cluster-signing-cert-file=/etc/kubernetes/pki/ca.pem \
- --cluster-signing-key-file=/etc/kubernetes/pki/ca-key.pem \
- --service-account-private-key-file=/etc/kubernetes/pki/sa.key \
- --kubeconfig=/etc/kubernetes/controller-manager.kubeconfig \
- --leader-elect=true \
- --use-service-account-credentials=true \
- --node-monitor-grace-period=40s \
- --node-monitor-period=5s \
- --pod-eviction-timeout=2m0s \
- --controllers=*,bootstrapsigner,tokencleaner \
- --allocate-node-cidrs=true \
- --cluster-cidr=172.16.0.0/12 \
- --requestheader-client-ca-file=/etc/kubernetes/pki/front-proxy-ca.pem \
- --node-cidr-mask-size=24
- Restart=always
- RestartSec=10s
- [Install]
- WantedBy=multi-user.target
所有Master节点启动kube-controller-manager
- systemctl daemon-reload
- systemctl enable --now kube-controller-manager
查看启动状态
- [root@k8s-master01 pki]# systemctl status kube-controller-manager
- ● kube-controller-manager.service - Kubernetes Controller Manager
- Loaded: loaded (/usr/lib/systemd/system/kube-controller-manager.service; enabled; vendor preset: disabled)
- Active: active (running) since Tue 2022-06-21 21:16:16 CST; 11s ago
- Docs: https://github.com/kubernetes/kubernetes
- Main PID: 4721 (kube-controller)
- Tasks: 5
- Memory: 27.4M
- CGroup: /system.slice/kube-controller-manager.service
- └─4721 /usr/local/bin/kube-controller-manager --v=2 --logtostderr=true --address=127.0.0.1 --root-ca-file=/etc/kubernetes/pki/ca.pem --cluster-signing-cert-file=/etc/kubernetes/pki/ca.pe...
- Jun 21 21:16:20 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:20.705608 4721 shared_informer.go:240] Waiting for caches to sync for ClusterRoleAggregator
- Jun 21 21:16:20 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:20.855590 4721 controllermanager.go:554] Started "pv-protection"
- Jun 21 21:16:20 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:20.855687 4721 controllermanager.go:539] Starting "replicaset"
- Jun 21 21:16:20 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:20.855787 4721 pv_protection_controller.go:83] Starting PV protection controller
- Jun 21 21:16:20 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:20.855807 4721 shared_informer.go:240] Waiting for caches to sync for PV protection
- Jun 21 21:16:21 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:21.015750 4721 controllermanager.go:554] Started "replicaset"
- Jun 21 21:16:21 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:21.015803 4721 controllermanager.go:539] Starting "nodeipam"
- Jun 21 21:16:21 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:21.015894 4721 replica_set.go:182] Starting replicaset controller
- Jun 21 21:16:21 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:21.015908 4721 shared_informer.go:240] Waiting for caches to sync for ReplicaSet
- Jun 21 21:16:21 k8s-master-lb kube-controller-manager[4721]: I0621 21:16:21.055523 4721 node_ipam_controller.go:91] Sending events to api server.
- [root@k8s-master01 pki]#
Scheduler
所有Master节点配置kube-scheduler service
- vi /usr/lib/systemd/system/kube-scheduler.service
- [Unit]
- Description=Kubernetes Scheduler
- Documentation=https://github.com/kubernetes/kubernetes
- After=network.target
- [Service]
- ExecStart=/usr/local/bin/kube-scheduler \
- --v=2 \
- --logtostderr=true \
- --address=127.0.0.1 \
- --leader-elect=true \
- --kubeconfig=/etc/kubernetes/scheduler.kubeconfig
- Restart=always
- RestartSec=10s
- [Install]
- WantedBy=multi-user.target
- systemctl daemon-reload
- systemctl enable --now kube-scheduler
TLS Bootstrapping配置
在Master01创建bootstrap
#注意,如果不是高可用集群,192.168.1.236:8443改为master01的地址,8443改为apiserver的端口,默认是6443
- cd /root/k8s-ha-install/bootstrap
- kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.pem --embed-certs=true --server=https://192.168.1.236:8443 --kubeconfig=/etc/kubernetes/bootstrap-kubelet.kubeconfig
- kubectl config set-credentials tls-bootstrap-token-user --token=c8ad9c.2e4d610cf3e7426e --kubeconfig=/etc/kubernetes/bootstrap-kubelet.kubeconfig
- kubectl config set-context tls-bootstrap-token-user@kubernetes --cluster=kubernetes --user=tls-bootstrap-token-user --kubeconfig=/etc/kubernetes/bootstrap-kubelet.kubeconfig
- kubectl config use-context tls-bootstrap-token-user@kubernetes --kubeconfig=/etc/kubernetes/bootstrap-kubelet.kubeconfig
注意:如果要修改boostrap.secret.yaml的token-id和token-secret,需要保证下图红圈内内的字符串一致的,并且位数是一样的。还要保证上个命令的黄色字体:c8ad9c.2e4d610cf3e7426e与你修改的字符串要一致

- mkdir -p /root/.kube; cp /etc/kubernetes/admin.kubeconfig /root/.kube/config
- kubectl create -f bootstrap.secret.yaml
Node节点配置
复制证书
Master01节点复制证书至Node节点
- cd /etc/kubernetes/
- for NODE in k8s-master02 k8s-master03 k8s-node01 k8s-node02; do
- ssh $NODE mkdir -p /etc/kubernetes/pki /etc/etcd/ssl /etc/etcd/ssl
- for FILE in etcd-ca.pem etcd.pem etcd-key.pem;do
- scp /etc/etcd/ssl/$FILE $NODE:/etc/etcd/ssl/
- done
- for FILE in pki/ca.pem pki/ca-key.pem pki/front-proxy-ca.pem bootstrap-kubelet.kubeconfig; do
- scp /etc/kubernetes/$FILE $NODE:/etc/kubernetes/${FILE}
- done
- done
Kubelet配置
所有节点创建相关目录
mkdir -p /var/lib/kubelet /var/log/kubernetes /etc/systemd/system/kubelet.service.d /etc/kubernetes/manifests/所有节点配置kubelet service
- vi /usr/lib/systemd/system/kubelet.service
- [Unit]
- Description=Kubernetes Kubelet
- Documentation=https://github.com/kubernetes/kubernetes
- After=docker.service
- Requires=docker.service
- [Service]
- ExecStart=/usr/local/bin/kubelet
- Restart=always
- StartLimitInterval=0
- RestartSec=10
- [Install]
- WantedBy=multi-user.target
所有节点配置kubelet service的配置文件
- vi /etc/systemd/system/kubelet.service.d/10-kubelet.conf
- [Service]
- Environment="KUBELET_KUBECONFIG_ARGS=--bootstrap-kubeconfig=/etc/kubernetes/bootstrap-kubelet.kubeconfig --kubeconfig=/etc/kubernetes/kubelet.kubeconfig"
- Environment="KUBELET_SYSTEM_ARGS=--network-plugin=cni --cni-conf-dir=/etc/cni/net.d --cni-bin-dir=/opt/cni/bin"
- Environment="KUBELET_CONFIG_ARGS=--config=/etc/kubernetes/kubelet-conf.yml --pod-infra-container-image=registry.cn-hangzhou.aliyuncs.com/google_containers/pause-amd64:3.2"
- Environment="KUBELET_EXTRA_ARGS=--node-labels=node.kubernetes.io/node=''"
- ExecStart=
- ExecStart=/usr/local/bin/kubelet $KUBELET_KUBECONFIG_ARGS $KUBELET_CONFIG_ARGS $KUBELET_SYSTEM_ARGS $KUBELET_EXTRA_ARGS
创建kubelet的配置文件
注意:如果更改了k8s的service网段,需要更改kubelet-conf.yml的clusterDNS:配置,改成k8s Service网段的第十个地址,比如10.96.0.10
- vi /etc/kubernetes/kubelet-conf.yml
- apiVersion: kubelet.config.k8s.io/v1beta1
- kind: KubeletConfiguration
- address: 0.0.0.0
- port: 10250
- readOnlyPort: 10255
- authentication:
- anonymous:
- enabled: false
- webhook:
- cacheTTL: 2m0s
- enabled: true
- x509:
- clientCAFile: /etc/kubernetes/pki/ca.pem
- authorization:
- mode: Webhook
- webhook:
- cacheAuthorizedTTL: 5m0s
- cacheUnauthorizedTTL: 30s
- cgroupDriver: systemd
- cgroupsPerQOS: true
- clusterDNS:
- - 10.96.0.10
- clusterDomain: cluster.local
- containerLogMaxFiles: 5
- containerLogMaxSize: 10Mi
- contentType: application/vnd.kubernetes.protobuf
- cpuCFSQuota: true
- cpuManagerPolicy: none
- cpuManagerReconcilePeriod: 10s
- enableControllerAttachDetach: true
- enableDebuggingHandlers: true
- enforceNodeAllocatable:
- - pods
- eventBurst: 10
- eventRecordQPS: 5
- evictionHard:
- imagefs.available: 15%
- memory.available: 100Mi
- nodefs.available: 10%
- nodefs.inodesFree: 5%
- evictionPressureTransitionPeriod: 5m0s
- failSwapOn: true
- fileCheckFrequency: 20s
- hairpinMode: promiscuous-bridge
- healthzBindAddress: 127.0.0.1
- healthzPort: 10248
- httpCheckFrequency: 20s
- imageGCHighThresholdPercent: 85
- imageGCLowThresholdPercent: 80
- imageMinimumGCAge: 2m0s
- iptablesDropBit: 15
- iptablesMasqueradeBit: 14
- kubeAPIBurst: 10
- kubeAPIQPS: 5
- makeIPTablesUtilChains: true
- maxOpenFiles: 1000000
- maxPods: 110
- nodeStatusUpdateFrequency: 10s
- oomScoreAdj: -999
- podPidsLimit: -1
- registryBurst: 10
- registryPullQPS: 5
- resolvConf: /etc/resolv.conf
- rotateCertificates: true
- runtimeRequestTimeout: 2m0s
- serializeImagePulls: true
- staticPodPath: /etc/kubernetes/manifests
- streamingConnectionIdleTimeout: 4h0m0s
- syncFrequency: 1m0s
- volumeStatsAggPeriod: 1m0s
启动所有节点kubelet
- systemctl daemon-reload
- systemctl enable --now kubelet
查看集群状态

kube-proxy配置
以下操作在Master01执行
- cd /root/k8s-ha-install
- kubectl -n kube-system create serviceaccount kube-proxy
- kubectl create clusterrolebinding system:kube-proxy --clusterrole system:node-proxier --serviceaccount kube-system:kube-proxy
- SECRET=$(kubectl -n kube-system get sa/kube-proxy --output=jsonpath='{.secrets[0].name}')
- JWT_TOKEN=$(kubectl -n kube-system get secret/$SECRET --output=jsonpath='{.data.token}'|base64 -d)
- PKI_DIR=/etc/kubernetes/pki
- K8S_DIR=/etc/kubernetes
- kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.pem --embed-certs=true --server=https://192.168.1.236:8443 --kubeconfig=${K8S_DIR}/kube-proxy.kubeconfig
- kubectl config set-credentials kubernetes --token=${JWT_TOKEN} --kubeconfig=/etc/kubernetes/kube-proxy.kubeconfig
- kubectl config set-context kubernetes --cluster=kubernetes --user=kubernetes --kubeconfig=/etc/kubernetes/kube-proxy.kubeconfig
- kubectl config use-context kubernetes --kubeconfig=/etc/kubernetes/kube-proxy.kubeconfig
在master01将kube-proxy的systemd Service文件发送到其他节点
如果更改了集群Pod的网段,需要更改
kube-proxy/kube-proxy.conf的clusterCIDR:172.16.0.0/12参数为Pod的网段。vi kube-proxy/kube-proxy.conf(在k8s-ha-install目录下执行)
- for NODE in k8s-master02 k8s-master03;do
- scp ${K8S_DIR}/kube-proxy.kubeconfig $NODE:/etc/kubernetes/kube-proxy.kubeconfig
- scp kube-proxy/kube-proxy.conf $NODE:/etc/kubernetes/kube-proxy.conf
- scp kube-proxy/kube-proxy.service $NODE:/usr/lib/systemd/system/kube-proxy.service
- done
- for NODE in k8s-node01 k8s-node02;do
- scp /etc/kubernetes/kube-proxy.kubeconfig $NODE:/etc/kubernetes/kube-proxy.kubeconfig
- scp kube-proxy/kube-proxy.conf $NODE:/etc/kubernetes/kube-proxy.conf
- scp kube-proxy/kube-proxy.service $NODE:/usr/lib/systemd/system/kube-proxy.service
- done
所有节点启动kube-proxy
- systemctl daemon-reload
- systemctl enable --now kube-proxy
安装Calico
以下步骤只在master01执行
cd /root/k8s-ha-install/calico/修改calico-etcd.yaml的以下位置
- sed -i 's#etcd_endpoints: "http://<ETCD_IP>:<ETCD_PORT>"#etcd_endpoints: "https://192.168.1.107:2379,https://192.168.1.108:2379,https://192.168.1.109:2379"#g' calico-etcd.yaml
- ETCD_CA=`cat /etc/kubernetes/pki/etcd/etcd-ca.pem | base64 | tr -d '\n'`
- ETCD_CERT=`cat /etc/kubernetes/pki/etcd/etcd.pem | base64 | tr -d '\n'`
- ETCD_KEY=`cat /etc/kubernetes/pki/etcd/etcd-key.pem | base64 | tr -d '\n'`
- sed -i "s@# etcd-key: null@etcd-key: ${ETCD_KEY}@g; s@# etcd-cert: null@etcd-cert: ${ETCD_CERT}@g; s@# etcd-ca: null@etcd-ca: ${ETCD_CA}@g" calico-etcd.yaml
- sed -i "s@# etcd-key: null@etcd-key: ${ETCD_KEY}@g; s@# etcd-cert: null@etcd-cert: ${ETCD_CERT}@g; s@# etcd-ca: null@etcd-ca: ${ETCD_CA}@g" calico-etcd.yaml
- set -i 's#etcd_ca: ""#etcd_ca: "/calico-secrets/etcd-ca"#g; s#etcd_cert: ""#etcd_cert: "/calico-secrets/etcd-cert"#g; s#etcd_key: "" #etcd_key: "/calico-secrets/etcd-key" #g' calico-etcd.yaml
- sed -i 's#etcd_ca: ""#etcd_ca: "/calico-secrets/etcd-ca"#g; s#etcd_cert: ""#etcd_cert: "/calico-secrets/etcd-cert"#g; s#etcd_key: "" #etcd_key: "/calico-secrets/etcd-key" #g' calico-etcd.yaml
- # 更改此处为自己的pod网段
- POD_SUBNET="172.16.0.0/12"
- sed -i 's@# - name: CALICO_IPV4POOL_CIDR@- name: CALICO_IPV4POOL_CIDR@g; s@# value: "192.168.0.0/16"@ value: '"${POD_SUBNET}"'@g' calico-etcd.yaml
kubectl apply -f calico-etcd.yaml查看容器状态

查看节点状态

安装CoreDNS
安装对应版本(推荐)
cd /root/k8s-ha-install/如果更改了k8s service的网段需要将coredns的serviceIP改成k8s service网段的第十个IP
sed -i "s#10.96.0.10#10.96.0.10#g" CoreDNS/coredns.yaml安装coredns
kubectl create -f CoreDNS/coredns.yaml安装最新版CoreDNS
- git clone https://github.com/coredns/deployment.git
- cd deployment/kubernetes
- ./deploy.sh -s -i 10.96.0.10 | kuberctl apply -f -
- 查看状态
- kubectl get pods -n kube-system -I k8s-app=kube-dns

安装Metrics Server
在新版的Kubernetes中系统资源的采集均使用Metrics-server,可以通过Metrics采集节点和Pod的内存、磁盘、CPU和网络的使用率。
安装metrics server
- cd /root/k8s-ha-install/metrics-server-0.4.x/
- kubectl create -f .
等待metrics server启动然后查看状态

安装dashboard
Dashboard部署
Dashboard用于展示集群中的各类资源,同时也可以通过Dashboard实时查看Pod的日志和在容器中执行一些命令等。
安装指定版本dashboard(推荐)
- cd /root/k8s-ha-install/dashboard/
- kubectl create -f .
安装最新版
官方Github地址:
https://github.com/kubernetes/dashboard可以在官方dashboard查看到最新版dashboard
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.3/aio/deploy/recommended.yaml
创建管理员用户vim admin.yaml
- apiVersion:v1
- kind: ServiceAccount
- metadata:
- name: admin-user
- namespace: kube-system
- ---
- apiVersion: rbac.authorization.k8s.io/v1
- kind: ClusterRoleBinding
- metadata:
- name: admin-user
- annotations:
- rbac.authorization.kubernetes.io/autoupdate: "true"
- roleRef:
- apiGroup: rbac.authorization.k8s.io
- kind: ClusterRole
- name: cluster-admin
- subjects:
- - kind: ServiceAccount
- name: admin-user
- namespace: kube-system
kubectl apply -f admin.yaml -n kube-system登录dashboard
在Chrome浏览器启动文件中加入启动参数,用于解决无法访问Dashboard的问题
--test-type --ignore-certificate-errors
更改dashboard的svc为NodePort:
kubectl edit svc kubernetes-dashboard -n kubernetes-dashboard
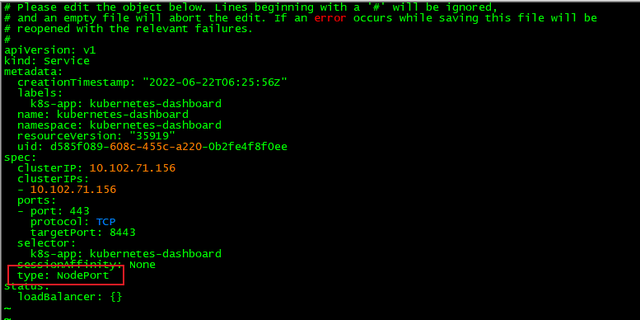
将ClusterIP更改为NodePort(如果已经为NodePort忽略此步骤):
查看端口号:
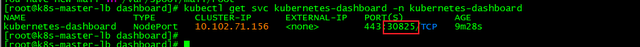
根据自己的实例端口号,通过任意安装了kube-proxy的宿主机或者VIP的IP+端口即可访问到dashboard:
访问dashboard:
https://192.168.1.236:30825/#/login,选择登录方式为令牌(即token方式)
查看token值
- [root@k8s-master-lb dashboard]# kubectl -n kube-system describe secret $(kubectl -n kube-system get secret | grep admin-user | awk '{print $1}')
- Name: admin-user-token-hzblx
- Namespace: kube-system
- Labels: <none>
- Annotations: kubernetes.io/service-account.name: admin-user
- kubernetes.io/service-account.uid: efd2583f-2cb9-4829-96e5-428901a2f931
- Type: kubernetes.io/service-account-token
- Data
- ====
- ca.crt: 1411 bytes
- namespace: 11 bytes
- token: eyJhbGciOiJSUzI1NiIsImtpZCI6IllRQVIxdm1zLWowdUp5aXdBdU9KNnBhbTQtMkhBRkJ1U092c0FvN0VPU3cifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJhZG1pbi11c2VyLXRva2VuLWh6Ymx4Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQubmFtZSI6ImFkbWluLXVzZXIiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiJlZmQyNTgzZi0yY2I5LTQ4MjktOTZlNS00Mjg5MDFhMmY5MzEiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6a3ViZS1zeXN0ZW06YWRtaW4tdXNlciJ9.gKfex-XB0Kj1B07d4duvKS3UHmXh2k17tda1HENefHGO92wz4mrYVdG6iwZ1L-_lbLgSYh-nD7XLr0DezvVgu-lb8JXYSlKNqoKlaG2w9FUtVgOxfrTJ_9o4PfiZUMbykGBUl4TwnPO4z6QQNEuCpuf1MEuxlCiXrMenYTTg4mtIMZMxXiZevTt69CNK5HboorCQ-_jArbzdRwevVuWzOP_3Sjv939X6pKyhUB0NE6tESywmvnZblpk8BNnY6wfWEPcJxwPYMPrlbZ3XHYH0Y63bo14MB-sC7lMzEOXTQioGA2IXNVDALcwwpvJ-1Ln7zqEtDfHJKg1cQsVr2tiKWA
- You have new mail in /var/spool/mail/root
- [root@k8s-master-lb dashboard]#
将token值输入到令牌后,单击登录即可访问Dashboard

-
相关阅读:
ELK日志分析系统叙述与部署,嘎嘎详细
P8352-[SDOI/SXOI2022]小N的独立集【dp套dp】
ThinkPHP 配置跨域请求,使用TP的内置跨域类配置,小程序和web网页跨域请求的区别及格式说明
Kafka之Producer网络传输
Vue中如何进行分布式任务调度与定时任务管理
HTML案例-3.表格练习
在linux服务器用git命令对比master和release分支变化,把改动的文件类名存入到一个文件里用java怎么实现
Sql Server 数据库事务与锁,同一事务更新又查询锁的变化,期望大家来解惑!
MySQL - 深入理解锁机制和实战场景
番外 1 : Java 环境下的 selenium 搭建
- 原文地址:https://blog.csdn.net/guolianggsta/article/details/125409347